Trend Micro Research on X: Scenario 2: If the user is not logged
Por um escritor misterioso
Last updated 12 fevereiro 2025
Trend Micro Ad Block One for Mac Data Collection Notice

The Myth of Air Purifier in Mitigating the Transmission Risk of SARS-CoV-2 Virus - Aerosol and Air Quality Research
How to generate various logs in Trend Micro for Windows
Some users does not appear in the HPU List - Trend Micro Cloud App Security
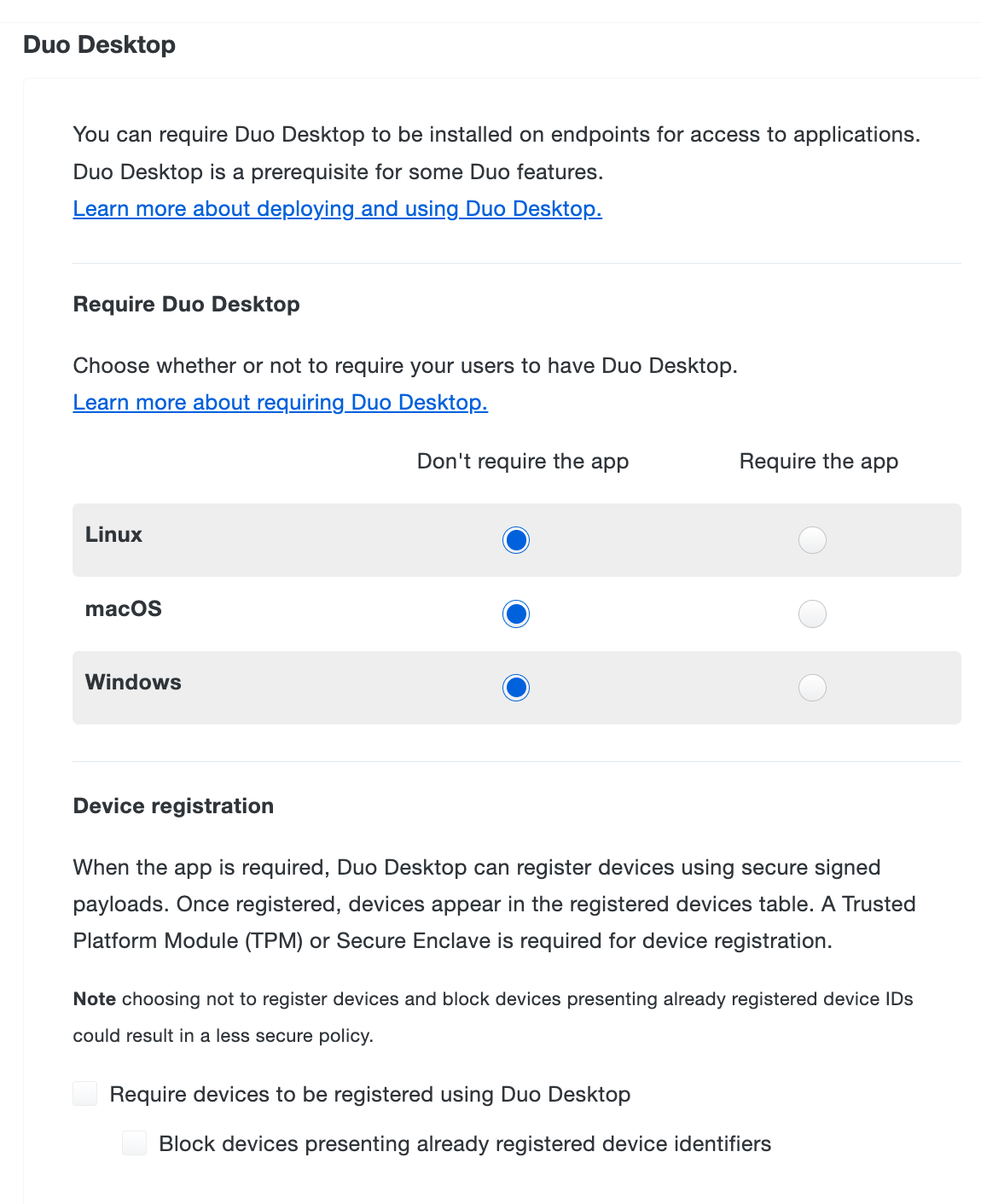
Duo Administration - Policy & Control
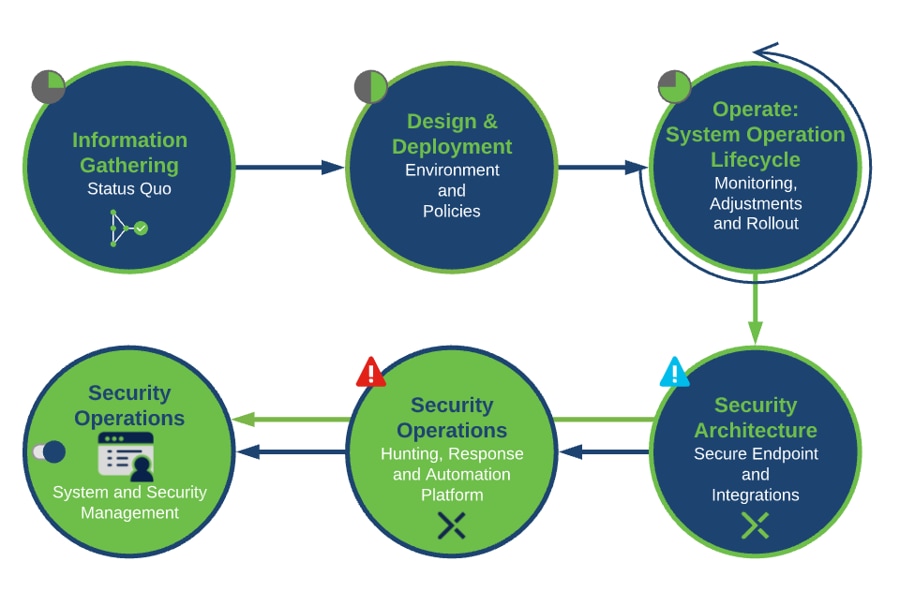
Secure Endpoint Best Practices Guide - Cisco

Trend Micro Deep Security 9.5 ( DSM ) -Part 1
Unable to install the Security Server. Setup did not find any local drive with free space' appears when upgrading the OfficeScan server
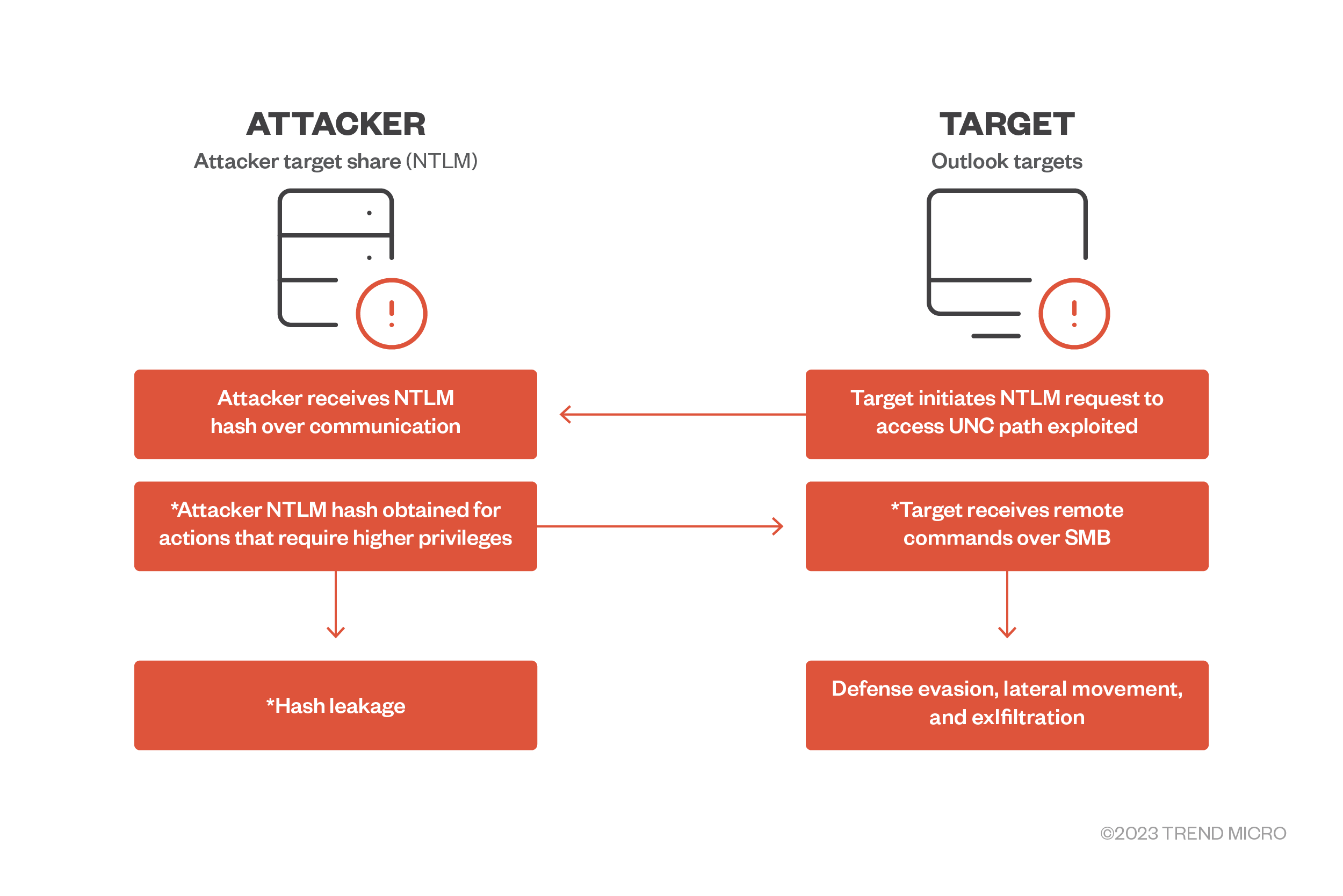
Patch CVE-2023-23397 Immediately: What You Need To Know and Do
Frontiers Block chain technology for digital financial inclusion in the industry 4.0, towards sustainable development?

Confusion Matrix: How To Use It & Interpret Results [Examples]
Cloaked Ursa (APT29) Hackers Use Trusted Online Storage Services
Recomendado para você
-
How to Log Into Facebook on Your Computer or Mobile Devices12 fevereiro 2025
-
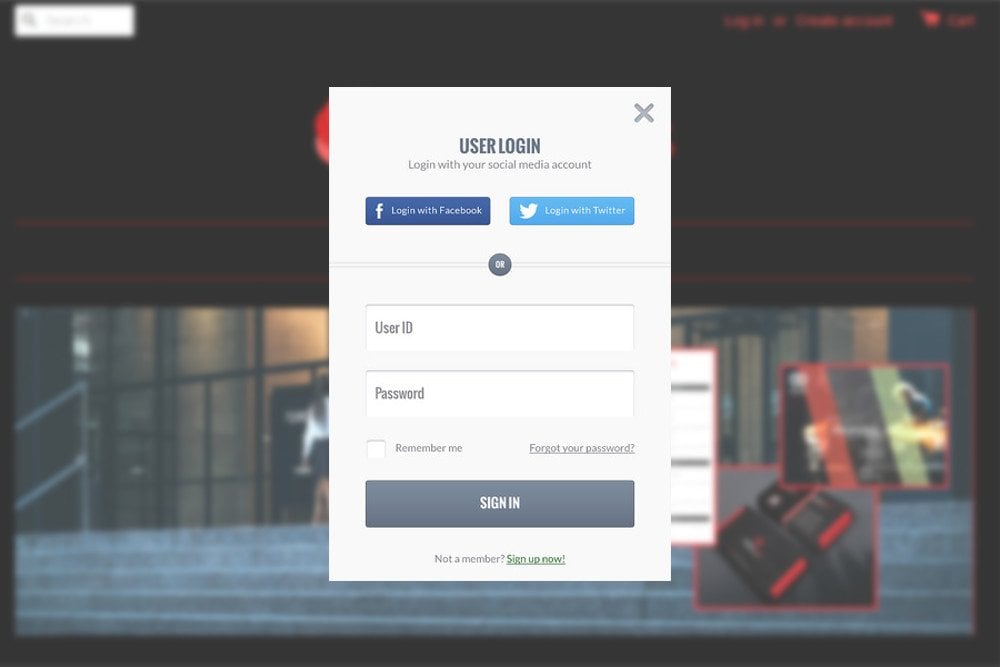 OAuth: How Does 'Login With Facebook/Google' Work? » Science ABC12 fevereiro 2025
OAuth: How Does 'Login With Facebook/Google' Work? » Science ABC12 fevereiro 2025 -
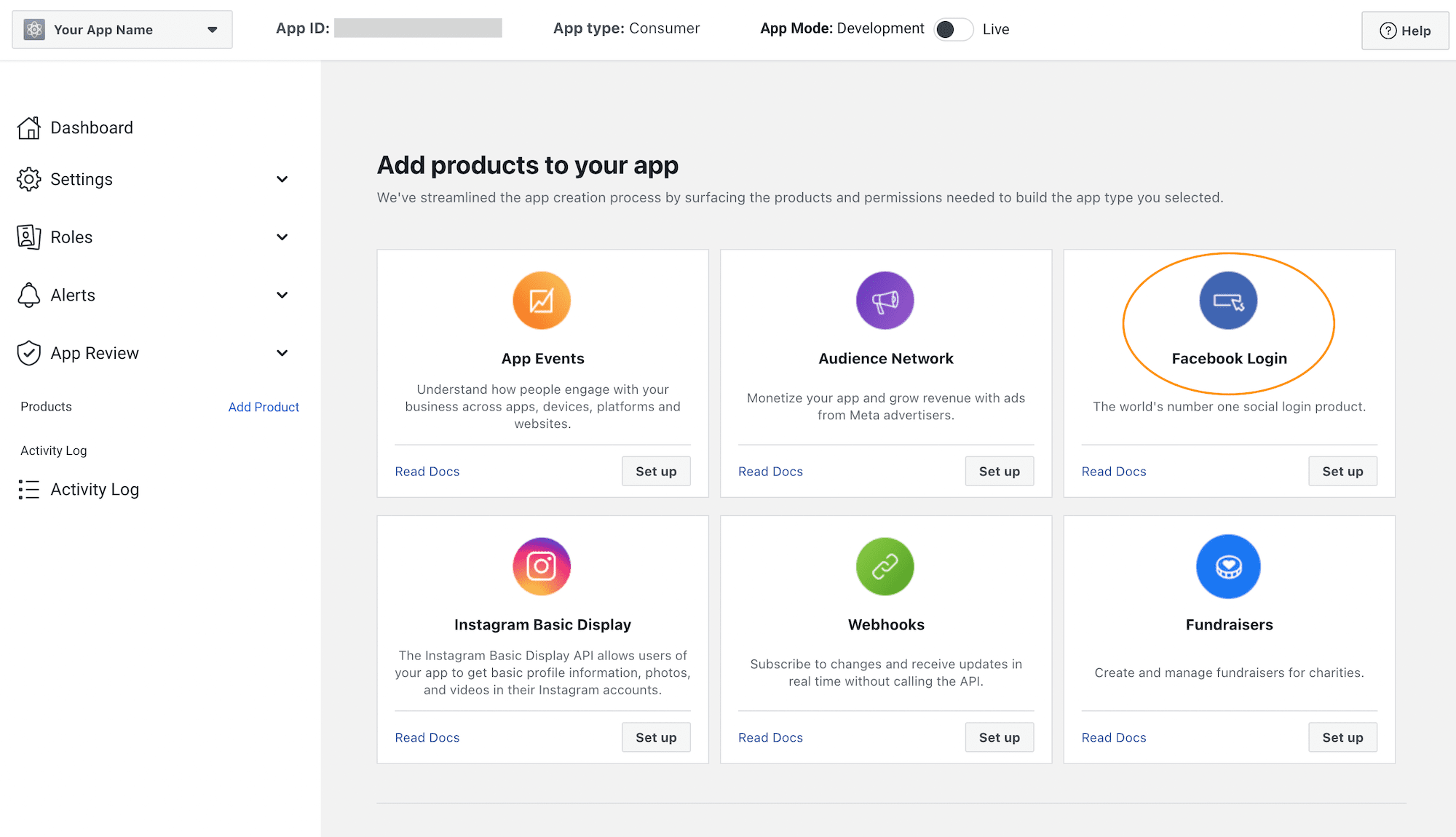 How To Add Facebook Login To Your Moodle 4.0+ Site - eLearning Themes12 fevereiro 2025
How To Add Facebook Login To Your Moodle 4.0+ Site - eLearning Themes12 fevereiro 2025 -
 Facebook login page redesign on Behance12 fevereiro 2025
Facebook login page redesign on Behance12 fevereiro 2025 -
 facebook login page12 fevereiro 2025
facebook login page12 fevereiro 2025 -
 ios - How to Display the Facebook login page when button is12 fevereiro 2025
ios - How to Display the Facebook login page when button is12 fevereiro 2025 -
 Facebook, social network, homepage with login mask, logo, internet12 fevereiro 2025
Facebook, social network, homepage with login mask, logo, internet12 fevereiro 2025 -
Facebook Lead Ad Forms Integration12 fevereiro 2025
-
 Facebook login page Stock Photo - Alamy12 fevereiro 2025
Facebook login page Stock Photo - Alamy12 fevereiro 2025 -
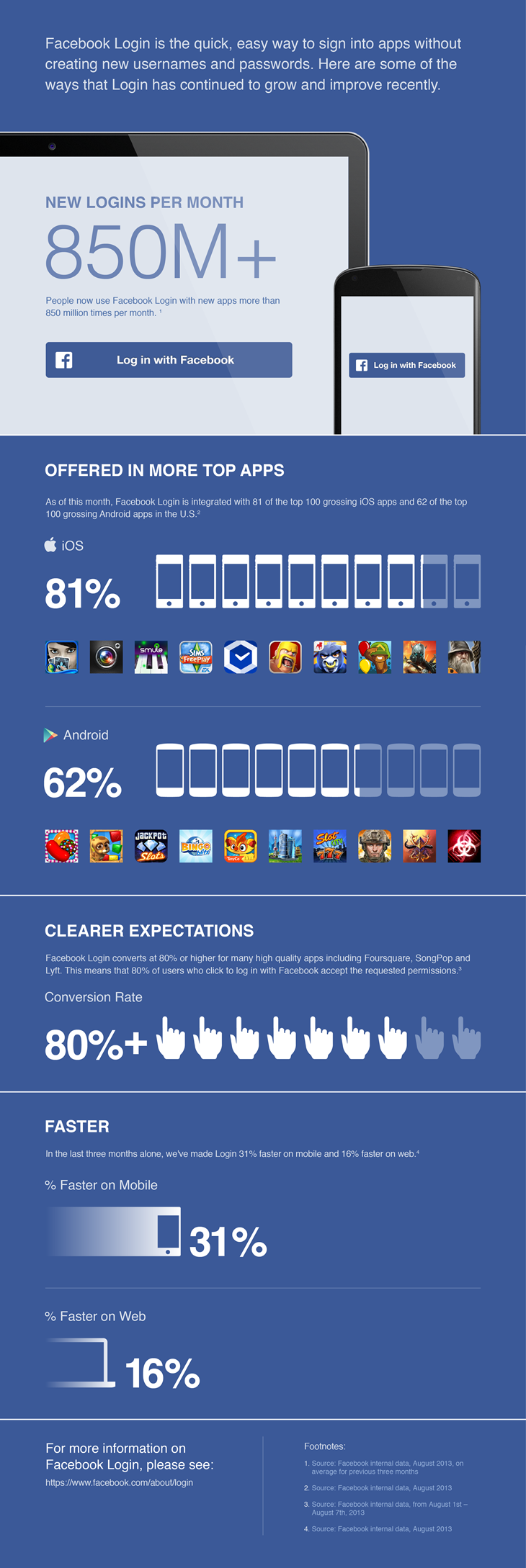 Updates to Facebook Login12 fevereiro 2025
Updates to Facebook Login12 fevereiro 2025
você pode gostar
-
 Jacksmith: Blacksmith Crafting Game Cool math y8'yı PC'ye indirin12 fevereiro 2025
Jacksmith: Blacksmith Crafting Game Cool math y8'yı PC'ye indirin12 fevereiro 2025 -
![Plugin] A plugin that makes gamepasses. Easy Pass Creator, Start](https://devforum-uploads.s3.dualstack.us-east-2.amazonaws.com/uploads/original/5X/d/1/c/c/d1cc0850f5f9d0cec402dd08cb76db1dcd7c7595.png) Plugin] A plugin that makes gamepasses. Easy Pass Creator, Start12 fevereiro 2025
Plugin] A plugin that makes gamepasses. Easy Pass Creator, Start12 fevereiro 2025 -
Snake.io é versão moderna do 'jogo da cobrinha' para iOS e12 fevereiro 2025
-
 The world's self-organizing economy can be expected to act strangely, as energy supplies deplete12 fevereiro 2025
The world's self-organizing economy can be expected to act strangely, as energy supplies deplete12 fevereiro 2025 -
 Buy Elfen Lied Lynn Okamoto [Volume 1-12 Manga Complete Set12 fevereiro 2025
Buy Elfen Lied Lynn Okamoto [Volume 1-12 Manga Complete Set12 fevereiro 2025 -
 How much elo did you get by winning all 10 matches in CS2? : r/GlobalOffensive12 fevereiro 2025
How much elo did you get by winning all 10 matches in CS2? : r/GlobalOffensive12 fevereiro 2025 -
 The Theater Equation : Ayreon: Movies & TV12 fevereiro 2025
The Theater Equation : Ayreon: Movies & TV12 fevereiro 2025 -
 FIFA 23: EA Play 10-Hour Free Trial Guide, Early Access! : r/FIFANEWS12 fevereiro 2025
FIFA 23: EA Play 10-Hour Free Trial Guide, Early Access! : r/FIFANEWS12 fevereiro 2025 -
Mayara Rodrigues Drawings - Vídeo novo no canal! FREEZA, CELL, MAJIN BOO - Dragon Ball Z Espero que gostem, link nos comentários!!12 fevereiro 2025
-
 Review: Layers of Fear 2 (Nintendo Switch) - Pure Nintendo12 fevereiro 2025
Review: Layers of Fear 2 (Nintendo Switch) - Pure Nintendo12 fevereiro 2025
