11 Types of Spoofing Attacks Every Security Professional Should
Por um escritor misterioso
Last updated 18 fevereiro 2025

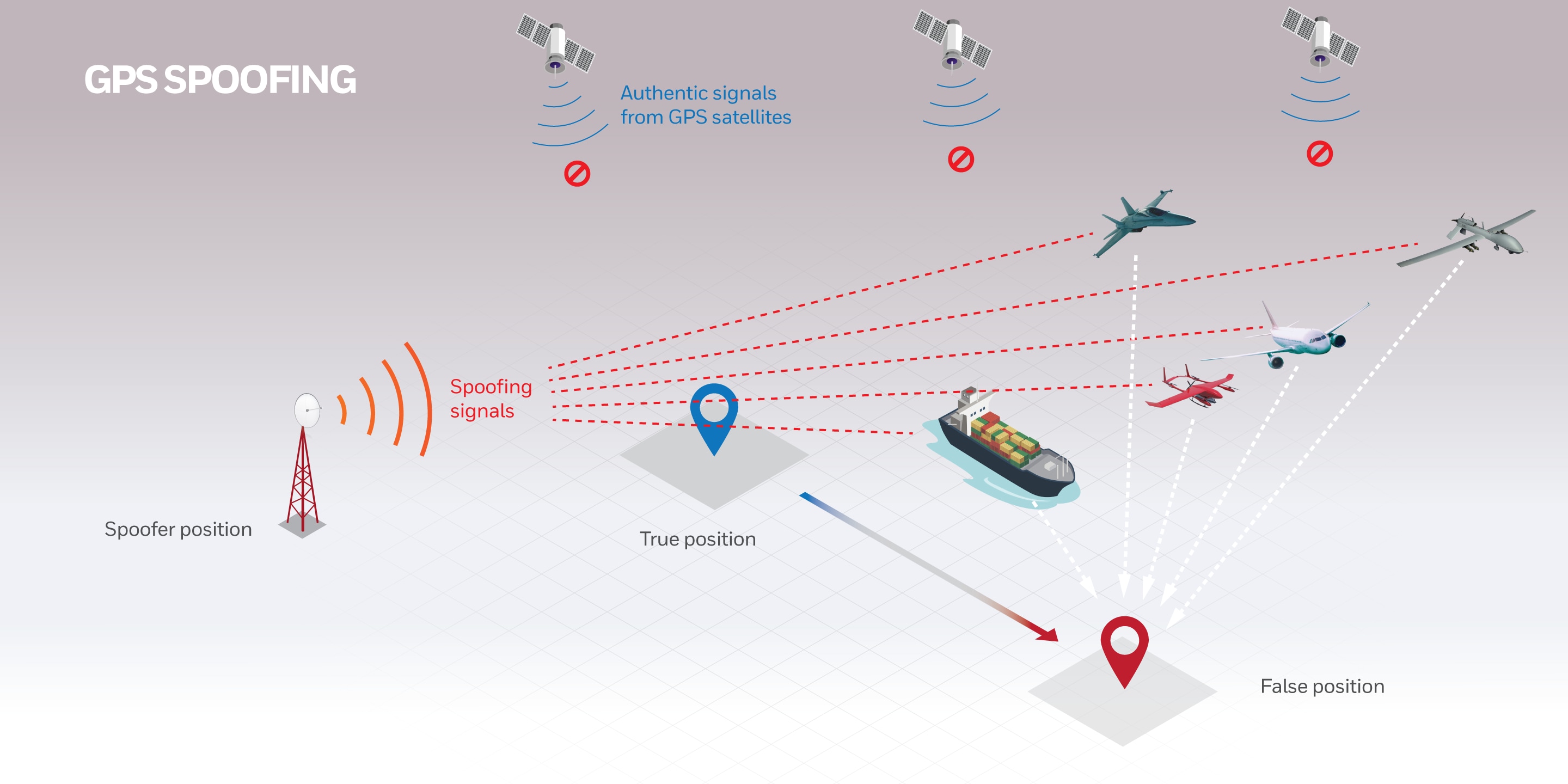
The term “spoofing” might have a comic implication in some contexts, but it’s no joke when it comes to information security. In fact, this is a subject matter of a whole separate chapter in a seasoned cybercriminal’s handbook. It comprises a multitude of techniques aimed at camouflaging a malicious actor or device as somebody or something else. The goal is to feign trust, gain a foothold in a system, get hold of data, pilfer money, or distribute predatory software. What can black hats try to . . .
The term “spoofing” might have a comic implication in some contexts, but it’s no joke when it comes to information security. In fact, this is a subject matter of a whole separate chapter in a seasoned cybercriminal’s handbook. It comprises a multitude of techniques aimed at camouflaging a malicious actor or device as somebody or something else. Out of all the nefarious scenarios that fit the mold of a spoofing attack, the following 11 types are growingly impactful for the enterprise these days.
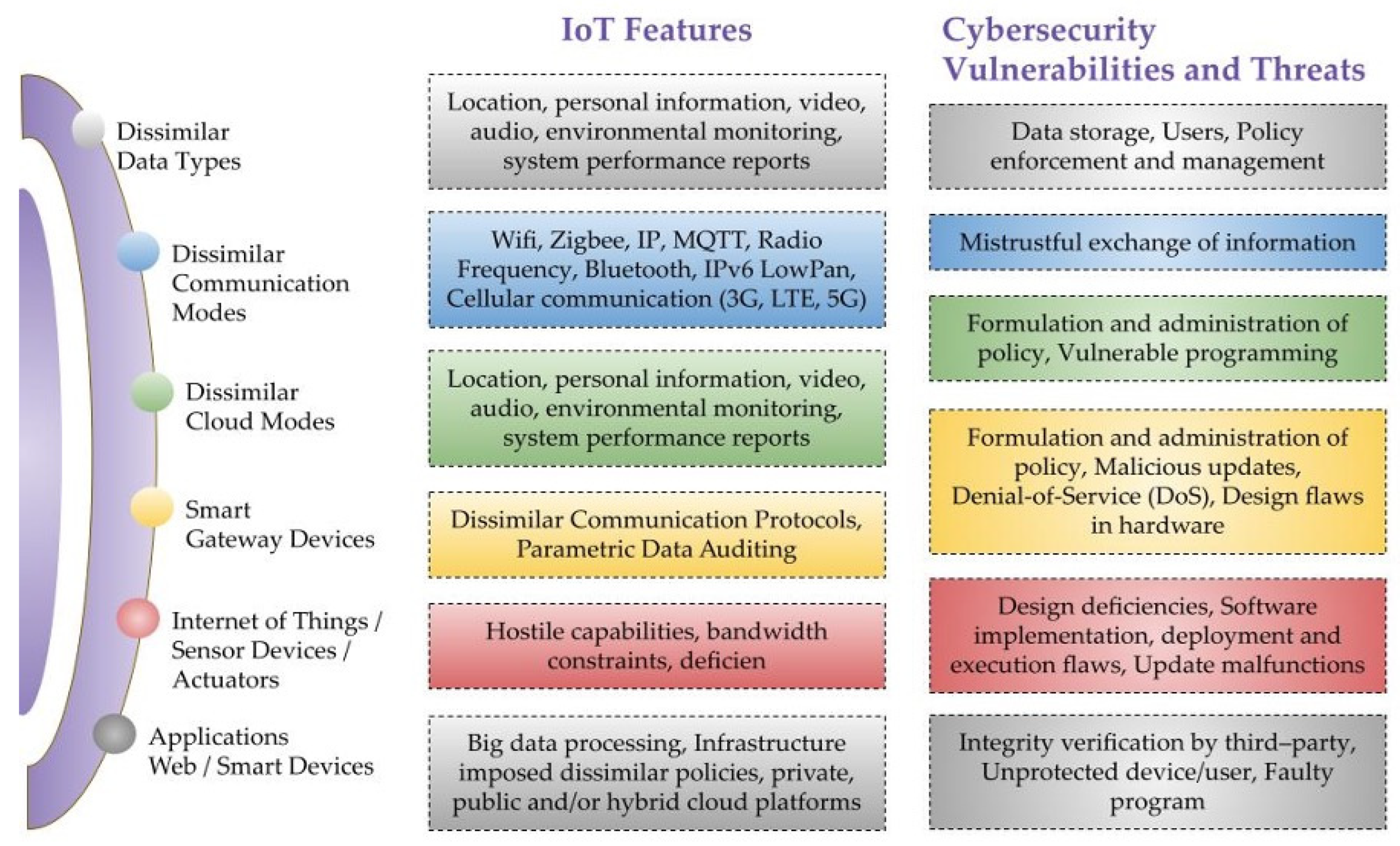
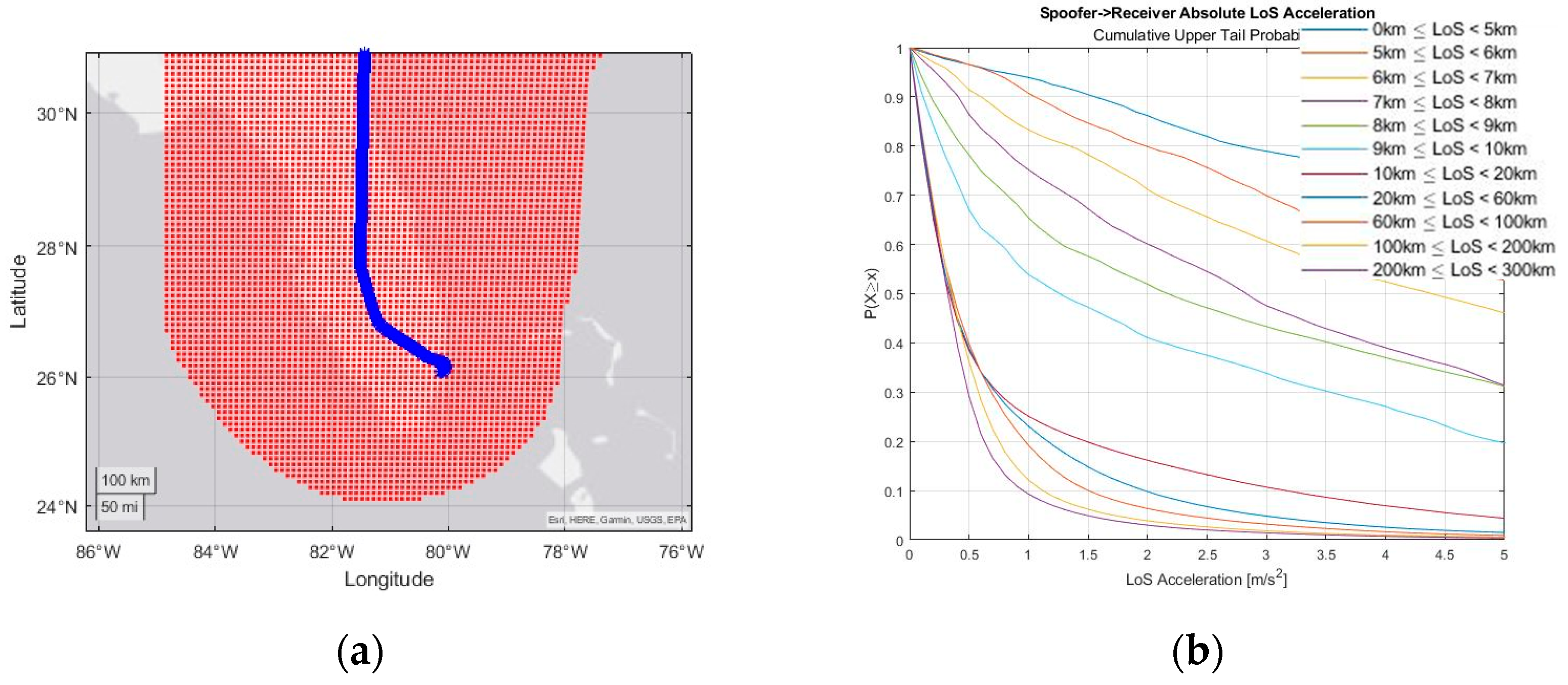
Sensors, Free Full-Text

7 Types of Spoofing Attacks And How To Detect Them

11 Types of Spoofing Attacks Every Security Professional Should
10 Steps to Cyber Security
Website spoofing: A definition + how spoofing works
Recomendado para você
-
 No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade18 fevereiro 2025
No GPS, No Problem: Honeywell Invents, Demonstrates Military-Grade18 fevereiro 2025 -
 CAIDA Catalog Search - A Collection of Scientific Research on the18 fevereiro 2025
CAIDA Catalog Search - A Collection of Scientific Research on the18 fevereiro 2025 -
 Visitor's Guide University of Arkansas18 fevereiro 2025
Visitor's Guide University of Arkansas18 fevereiro 2025 -
 GootBot - Gootloader's new approach to post-exploitation18 fevereiro 2025
GootBot - Gootloader's new approach to post-exploitation18 fevereiro 2025 -
 Engineering Proceedings, Free Full-Text18 fevereiro 2025
Engineering Proceedings, Free Full-Text18 fevereiro 2025 -
RoDAR the Equaliser18 fevereiro 2025
-
Red Engine Un Ban18 fevereiro 2025
-
![Release] rainbow - EFI bootkit like HWID spoofer (SMBIOS/disk/NIC)](https://i.imgur.com/r8xNj4f.png) Release] rainbow - EFI bootkit like HWID spoofer (SMBIOS/disk/NIC)18 fevereiro 2025
Release] rainbow - EFI bootkit like HWID spoofer (SMBIOS/disk/NIC)18 fevereiro 2025 -
 Pokemod Devs released info on what they believe is behind the most18 fevereiro 2025
Pokemod Devs released info on what they believe is behind the most18 fevereiro 2025 -
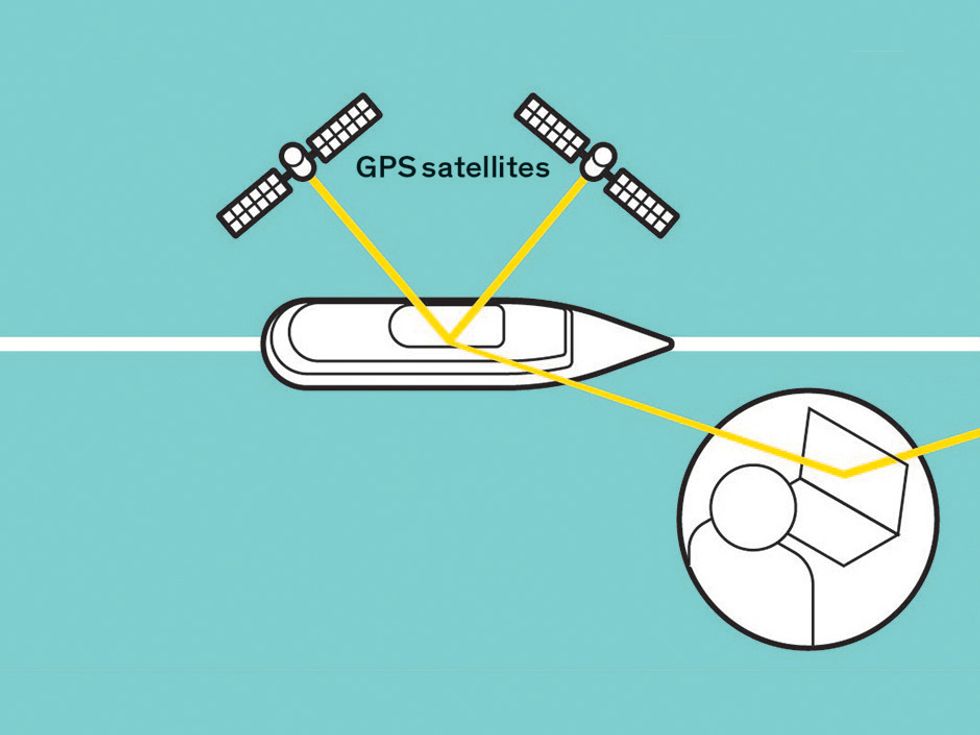 Protecting GPS From Spoofers Is Critical to the Future of18 fevereiro 2025
Protecting GPS From Spoofers Is Critical to the Future of18 fevereiro 2025
você pode gostar
-
 Tudo o que você precisa saber sobre areia movediça - e como sobreviver a ela - TecMundo18 fevereiro 2025
Tudo o que você precisa saber sobre areia movediça - e como sobreviver a ela - TecMundo18 fevereiro 2025 -
 Is Assassin's Creed Mirage on Xbox Game Pass?18 fevereiro 2025
Is Assassin's Creed Mirage on Xbox Game Pass?18 fevereiro 2025 -
 ALL NEW *SECRET* CODES in SEA PIECE CODES! (Sea Piece Codes18 fevereiro 2025
ALL NEW *SECRET* CODES in SEA PIECE CODES! (Sea Piece Codes18 fevereiro 2025 -
 This opinion on Bayonetta Origins on Metacritic might be one of the18 fevereiro 2025
This opinion on Bayonetta Origins on Metacritic might be one of the18 fevereiro 2025 -
 Violence Erupts Between Armenia And Azerbaijan Over Long-Disputed Region : NPR18 fevereiro 2025
Violence Erupts Between Armenia And Azerbaijan Over Long-Disputed Region : NPR18 fevereiro 2025 -
 Casas à venda em Alto da Boa Vista, Londrina - PR, 86030-03018 fevereiro 2025
Casas à venda em Alto da Boa Vista, Londrina - PR, 86030-03018 fevereiro 2025 -
 EFootball 2022 - Análise18 fevereiro 2025
EFootball 2022 - Análise18 fevereiro 2025 -
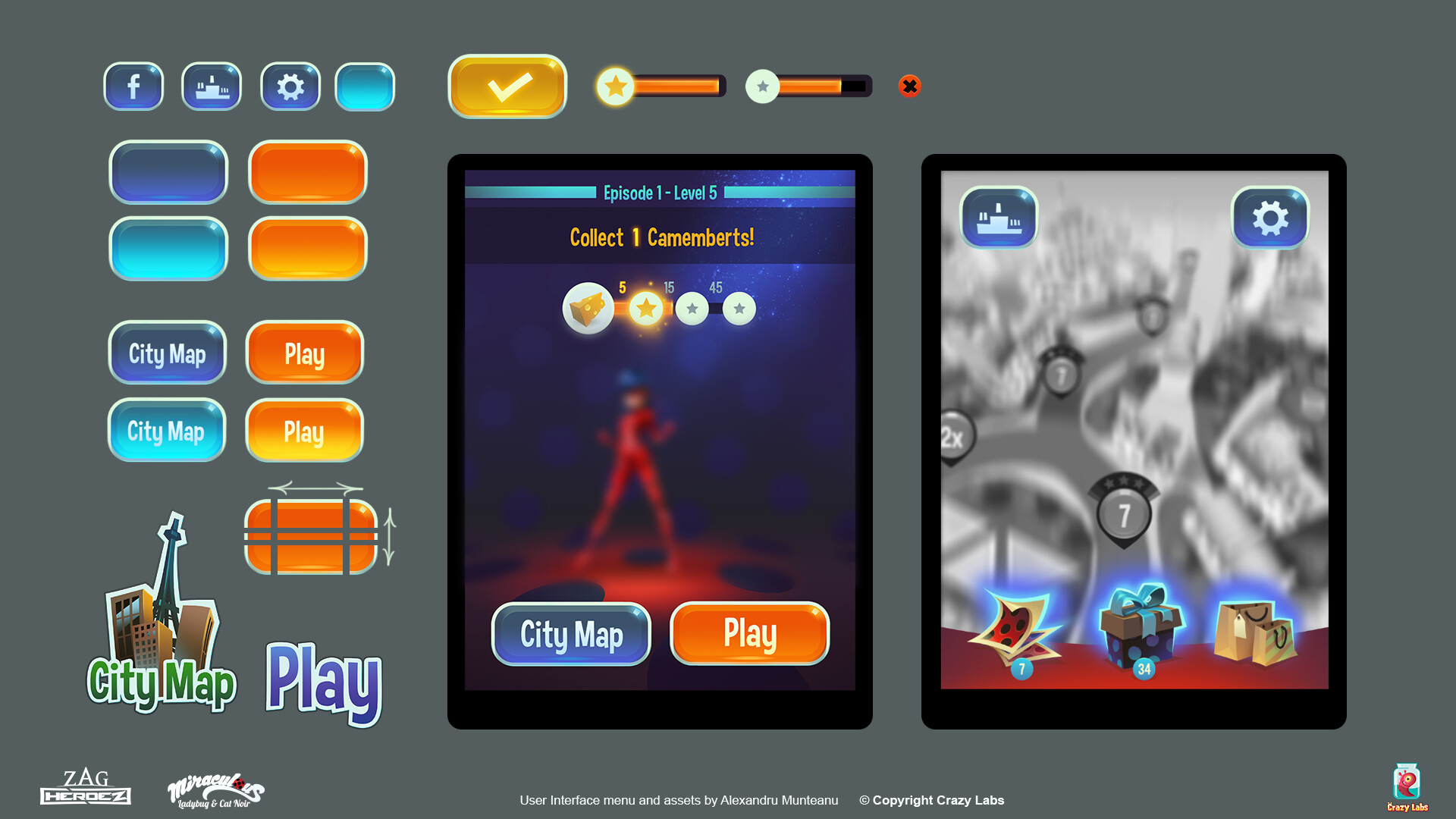 ArtStation - Miraculous Ladybug Mobile Game - UI Elements18 fevereiro 2025
ArtStation - Miraculous Ladybug Mobile Game - UI Elements18 fevereiro 2025 -
Hehe come play with me”~Sally - Creepypasta Crew18 fevereiro 2025
-
 Google Play $50 Gift Card Google Play 50 2022 - Best Buy18 fevereiro 2025
Google Play $50 Gift Card Google Play 50 2022 - Best Buy18 fevereiro 2025


