SILKLOADER: How Hackers Evade Detection
Por um escritor misterioso
Last updated 27 fevereiro 2025

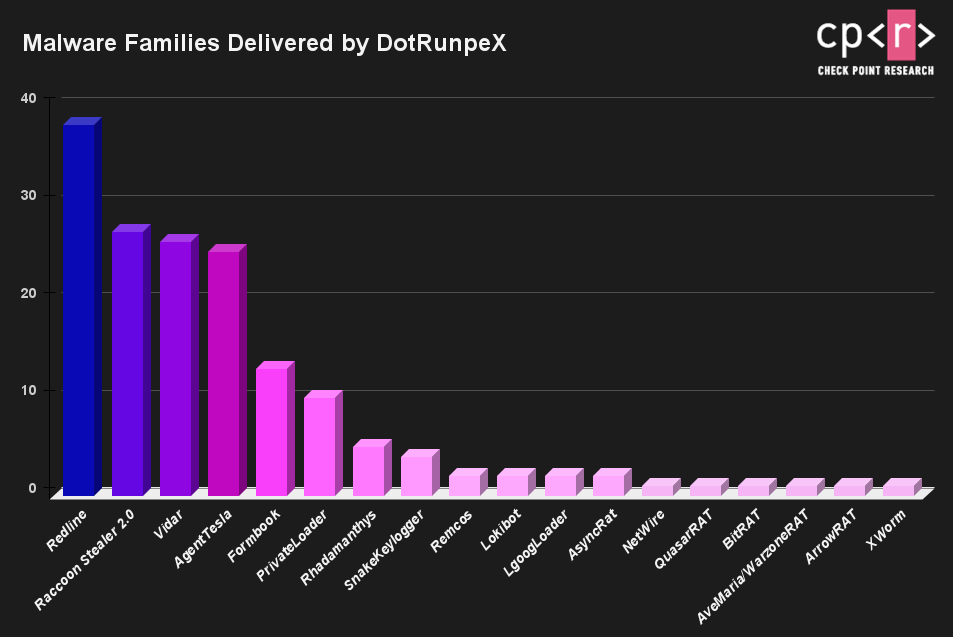
As the cyber threat landscape continues to evolve, hackers are employing increasingly sophisticated techniques to evade detection. One such example is the SILKLOADER malware, which has recently gained attention for its stealth capabilities.

Evading AV with Veil-Evasion
Risky Biz News: Google wants to reduce lifespan of TLS certificates from one year to just 90 days

Endpoint Protection - Symantec Enterprise

Hackread - Latest Cybersecurity News, Press Releases & Technology Today

Chinese Silkloader cyber attack tool falls into Russian hands

Cl0p hits Hitachi Energy. TikTok surveillance investigated. BreachForums arrest. Hacktivists, torrents in the hybrid war.

How Hackers Are “Blending In” to Evade Detection

Evading AV with Veil-Evasion

Chinese State-Sponsored Hackers Evade Common Cybersecurity Tools

Pakistani Power Firms urged to establish Cyber Security guidelines

How Hackers Are “Blending In” to Evade Detection

OSINTer - Article List
Recomendado para você
-
 BEST Roblox Evade Script GUI ESP Exploit Unpatched (2023 Pastebin27 fevereiro 2025
BEST Roblox Evade Script GUI ESP Exploit Unpatched (2023 Pastebin27 fevereiro 2025 -
 Evade Script Auto Farm & Esp Gui - Updated Pastebin Script27 fevereiro 2025
Evade Script Auto Farm & Esp Gui - Updated Pastebin Script27 fevereiro 2025 -
![NEW] Evade Script / Hack GUI, God Mode](https://i.ytimg.com/vi/nHcDYO46Ib8/maxresdefault.jpg) NEW] Evade Script / Hack GUI, God Mode27 fevereiro 2025
NEW] Evade Script / Hack GUI, God Mode27 fevereiro 2025 -
evade script|TikTok Search27 fevereiro 2025
-
![Evade [Auto Farm - Fast Revive & More!] Scripts](https://rbxscript.com/images/-nOtc6We36d-image.jpg) Evade [Auto Farm - Fast Revive & More!] Scripts27 fevereiro 2025
Evade [Auto Farm - Fast Revive & More!] Scripts27 fevereiro 2025 -
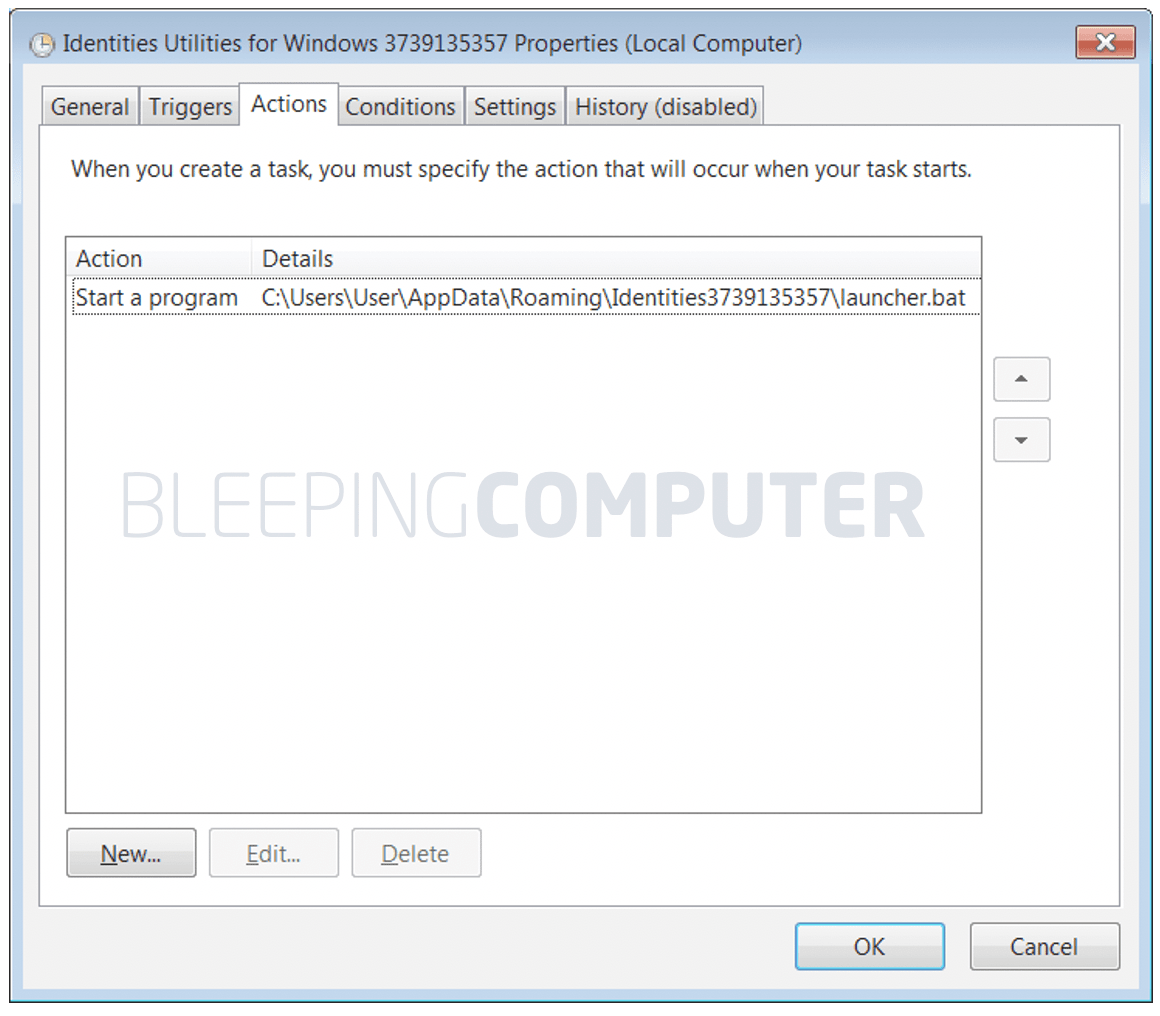 TrickBot malware uses obfuscated Windows batch script to evade27 fevereiro 2025
TrickBot malware uses obfuscated Windows batch script to evade27 fevereiro 2025 -
evade script delta|TikTok Search27 fevereiro 2025
-
 Evade Script Pastebin Hacks: Auto Farm, Attack, ESP & More!27 fevereiro 2025
Evade Script Pastebin Hacks: Auto Farm, Attack, ESP & More!27 fevereiro 2025 -
evade script template|TikTok Search27 fevereiro 2025
-
 evade fly script|TikTok Search27 fevereiro 2025
evade fly script|TikTok Search27 fevereiro 2025
você pode gostar
-
 The Asterisk War (Season 1) Review27 fevereiro 2025
The Asterisk War (Season 1) Review27 fevereiro 2025 -
 TÊNIS MAD RATS HI-TOP PRETO/GRAFITE - KOLONI SKATESHOP27 fevereiro 2025
TÊNIS MAD RATS HI-TOP PRETO/GRAFITE - KOLONI SKATESHOP27 fevereiro 2025 -
 Uncomfortable Laughter: Revisiting Funny Games (1997) on Criterion27 fevereiro 2025
Uncomfortable Laughter: Revisiting Funny Games (1997) on Criterion27 fevereiro 2025 -
 Slither.io GIANT SNAKE with FinsGames27 fevereiro 2025
Slither.io GIANT SNAKE with FinsGames27 fevereiro 2025 -
 Меню ресторана Ponto X Lanches, xis, hamburguer - Bento Gonçalves RS., Bento Gonçalves27 fevereiro 2025
Меню ресторана Ponto X Lanches, xis, hamburguer - Bento Gonçalves RS., Bento Gonçalves27 fevereiro 2025 -
 Monster lvl 999 for Melon Playground27 fevereiro 2025
Monster lvl 999 for Melon Playground27 fevereiro 2025 -
 Pinhão: rico em fibras, semente ajuda no funcionamento do intestino27 fevereiro 2025
Pinhão: rico em fibras, semente ajuda no funcionamento do intestino27 fevereiro 2025 -
 CRP-03 - #ImplementaLei13935: CRP-03 e CRESS-BA realizam audiência pública com participação de instituições vinculadas à educação27 fevereiro 2025
CRP-03 - #ImplementaLei13935: CRP-03 e CRESS-BA realizam audiência pública com participação de instituições vinculadas à educação27 fevereiro 2025 -
 Itana Grbić: A big plus is that we will play the group at home27 fevereiro 2025
Itana Grbić: A big plus is that we will play the group at home27 fevereiro 2025 -
 HappinessCharge PreCure! - Wikiwand27 fevereiro 2025
HappinessCharge PreCure! - Wikiwand27 fevereiro 2025


