PDF] Power Consumption-based Detection of Sabotage Attacks in
Por um escritor misterioso
Last updated 28 fevereiro 2025
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/4-Figure1-1.png)
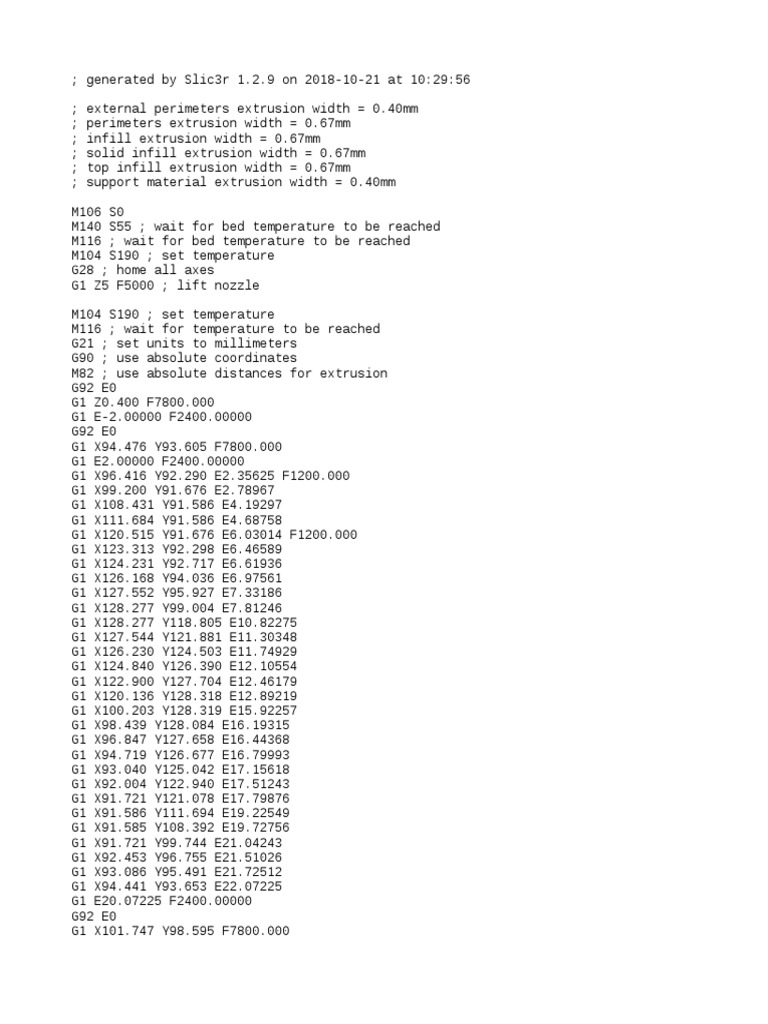
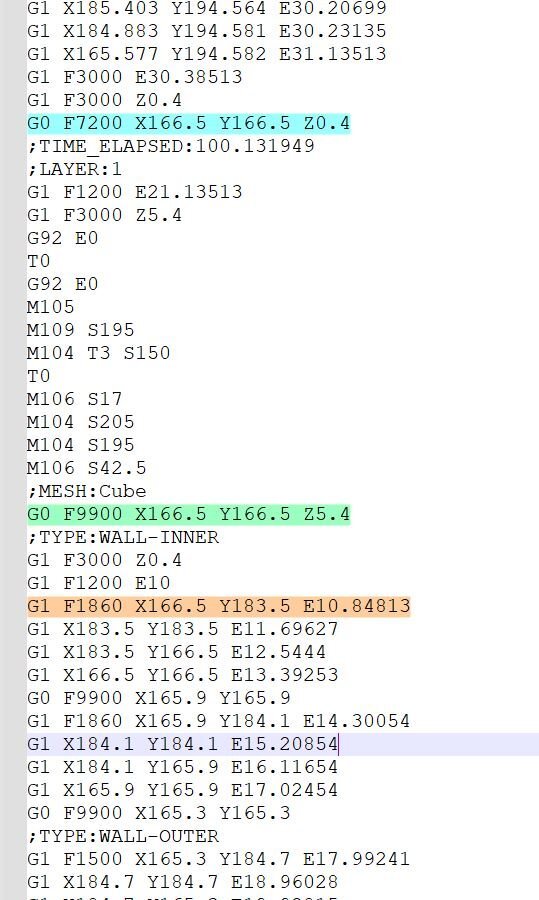
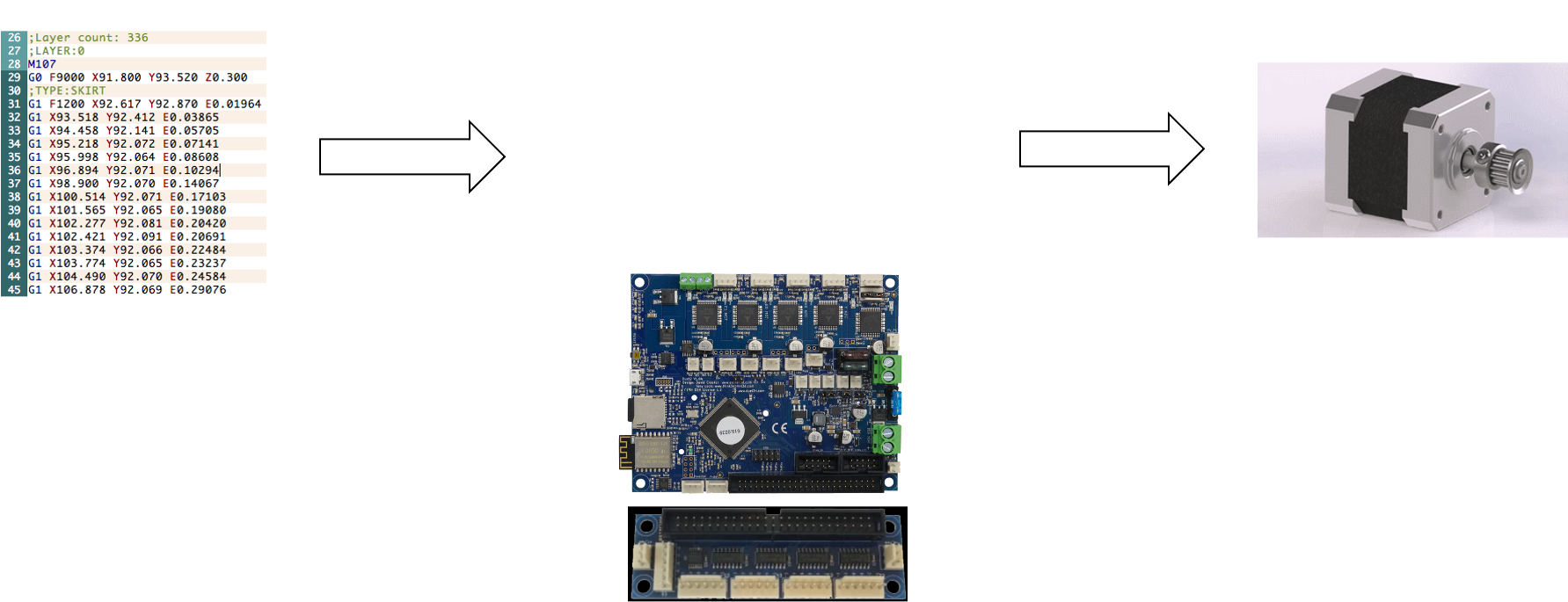
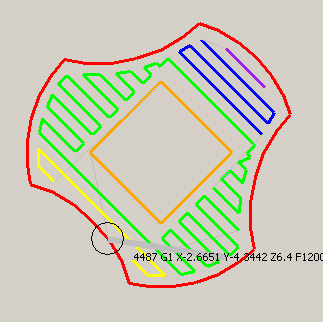
This work proposes a novel approach for detecting sabotage attacks in additive Manufacturing, based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. Additive Manufacturing (AM), a.k.a. 3D Printing, is increasingly used to manufacture functional parts of safety-critical systems. AM's dependence on computerization raises the concern that the AM process can be tampered with, and a part's mechanical properties sabotaged. This can lead to the destruction of a system employing the sabotaged part, causing loss of life, financial damage, and reputation loss. To address this threat, we propose a novel approach for detecting sabotage attacks. Our approach is based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. The proposed approach has numerous advantages: (i) it is non-invasive in a time-critical process, (ii) it can be retrofitted in legacy systems, and (iii) it is airgapped from the computerized components of the AM process, preventing simultaneous compromise. Evaluation on a desktop 3D Printer detects all attacks involving a modification of X or Y motor movement, with false positives at 0%.
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.researchgate.net/profile/Shih-Yuan-Yu/publication/339059143/figure/fig4/AS:855393400004611@1580953087286/Original-and-modified-wrench_Q320.jpg)
PDF) Sabotage Attack Detection for Additive Manufacturing Systems
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pyimagesearch.com/wp-content/uploads/2022/08/DER.png)
Computer Vision and Deep Learning for Electricity - PyImageSearch
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.mdpi.com/sensors/sensors-22-04662/article_deploy/html/images/sensors-22-04662-g001-550.jpg)
Sensors, Free Full-Text
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0278612522000632-gr3.jpg)
Physics-based detection of cyber-attacks in manufacturing systems: A machining case study - ScienceDirect
Full article: Black start: the risk of grid failure from a cyber attack and the policies needed to prepare for it
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/9-Table1-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.imperva.com/learn/wp-content/uploads/sites/13/2021/10/cyberwarfare.png)
What is Cyber Warfare, Types, Examples & Mitigation
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.researchgate.net/profile/Mark-Yampolskiy/publication/319524597/figure/fig1/AS:535794353356802@1504754736685/Considered-Threat-Model_Q320.jpg)
PDF) Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0278612518300463-gr6.jpg)
Security of smart manufacturing systems - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://imgv2-2-f.scribdassets.com/img/document/85577319/298x396/ea43c77ec6/1378525595?v=1)
Case Study of Insider Sabotage, PDF, Computer Security
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://pubs.acs.org/cms/10.1021/acsnano.1c10635/asset/images/acsnano.1c10635.social.jpeg_v03)
Nanotechnology Tools Enabling Biological Discovery
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://webobjects2.cdw.com/is/image/CDW/MKT25380_solution-spotlight-medLar_thumbnail)
Solution in Action, How Vulnerable is Your SCADA System, Energy
Recomendado para você
-
 Cura 5.3 unnecessary move after toolchange in gcode - UltiMaker28 fevereiro 2025
Cura 5.3 unnecessary move after toolchange in gcode - UltiMaker28 fevereiro 2025 -
 IMProVe - Simufact software solutions28 fevereiro 2025
IMProVe - Simufact software solutions28 fevereiro 2025 -
SOLVED) V-Engrave & UCCNC problem28 fevereiro 2025
-
 Noa Samarelli28 fevereiro 2025
Noa Samarelli28 fevereiro 2025 -
 HydraRaptor: Buried nuts and hanging holes28 fevereiro 2025
HydraRaptor: Buried nuts and hanging holes28 fevereiro 2025 -
20mm Calibration Cube, PDF, Alternative Energy28 fevereiro 2025
-
 A Variety of Observations and Complaints - Bambu Lab X1 Series28 fevereiro 2025
A Variety of Observations and Complaints - Bambu Lab X1 Series28 fevereiro 2025 -
 Extra Retraction at Start - UltiMaker Cura - UltiMaker Community28 fevereiro 2025
Extra Retraction at Start - UltiMaker Cura - UltiMaker Community28 fevereiro 2025 -
 ultimaker cura - How center the nozzle before start printing - 3D28 fevereiro 2025
ultimaker cura - How center the nozzle before start printing - 3D28 fevereiro 2025 -
 Rectract Before Outer Wall not working - ZScar issues - UltiMaker28 fevereiro 2025
Rectract Before Outer Wall not working - ZScar issues - UltiMaker28 fevereiro 2025
você pode gostar
-
trading tier list blox fruits|TikTok Search28 fevereiro 2025
-
The Crew™ Motorfest Standard Edition - Cross-Gen Bundle Xbox One — buy online and track price history — XB Deals USA28 fevereiro 2025
-
 Bonecos Sonic Collection Grande 25cm Caixa Original Azul, Magalu Empresas28 fevereiro 2025
Bonecos Sonic Collection Grande 25cm Caixa Original Azul, Magalu Empresas28 fevereiro 2025 -
 Lupica: Playing the what-if game with the Jets and Giants28 fevereiro 2025
Lupica: Playing the what-if game with the Jets and Giants28 fevereiro 2025 -
 Chisel Reborn - Minecraft Mods - CurseForge28 fevereiro 2025
Chisel Reborn - Minecraft Mods - CurseForge28 fevereiro 2025 -
 Pin on Highschool dxd28 fevereiro 2025
Pin on Highschool dxd28 fevereiro 2025 -
 Buy Gran Turismo 7 - Pre-Order Bonus PS5 PlayStation 5 PlayStation Key28 fevereiro 2025
Buy Gran Turismo 7 - Pre-Order Bonus PS5 PlayStation 5 PlayStation Key28 fevereiro 2025 -
Shai Nemesh - Human Resources Director - Wolfoods, Inc.28 fevereiro 2025
-
 Jogo de Dama Turma da Mônica - Babebi28 fevereiro 2025
Jogo de Dama Turma da Mônica - Babebi28 fevereiro 2025 -
 Roblox Fruit Battlegrounds Tier List (2023) - Games Adda28 fevereiro 2025
Roblox Fruit Battlegrounds Tier List (2023) - Games Adda28 fevereiro 2025