Malware analysis Malicious activity
Por um escritor misterioso
Last updated 02 abril 2025
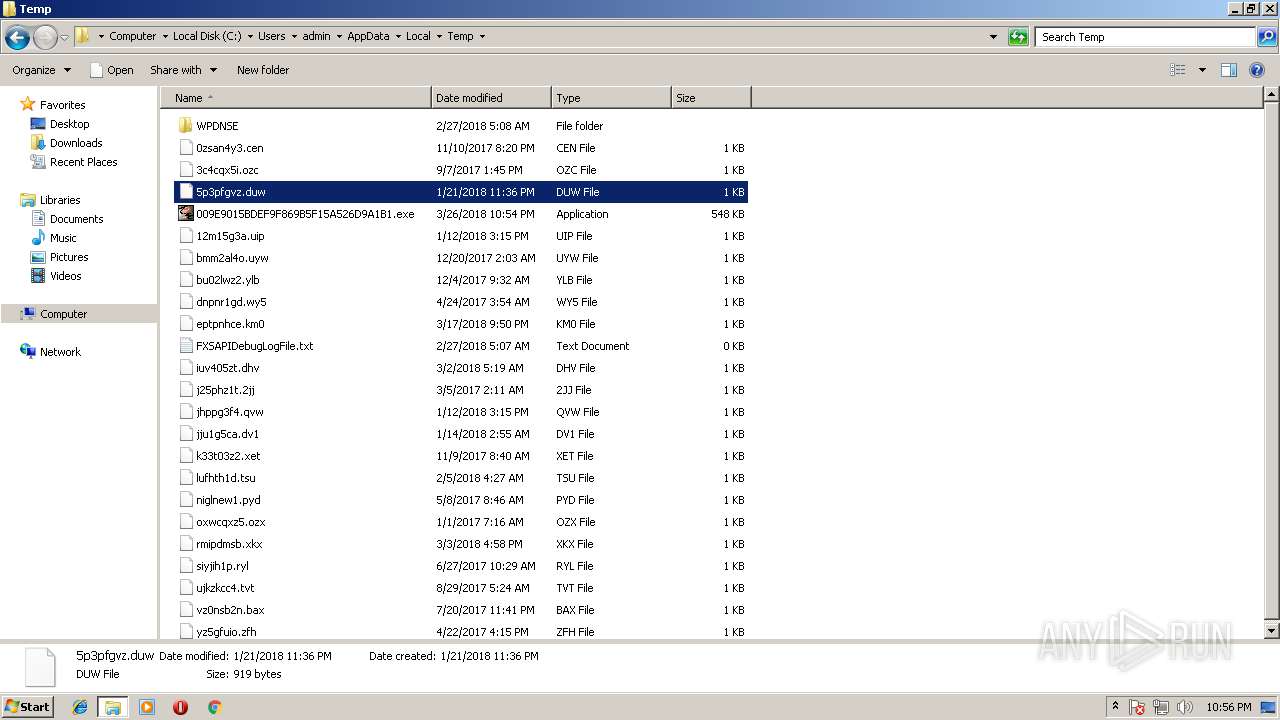
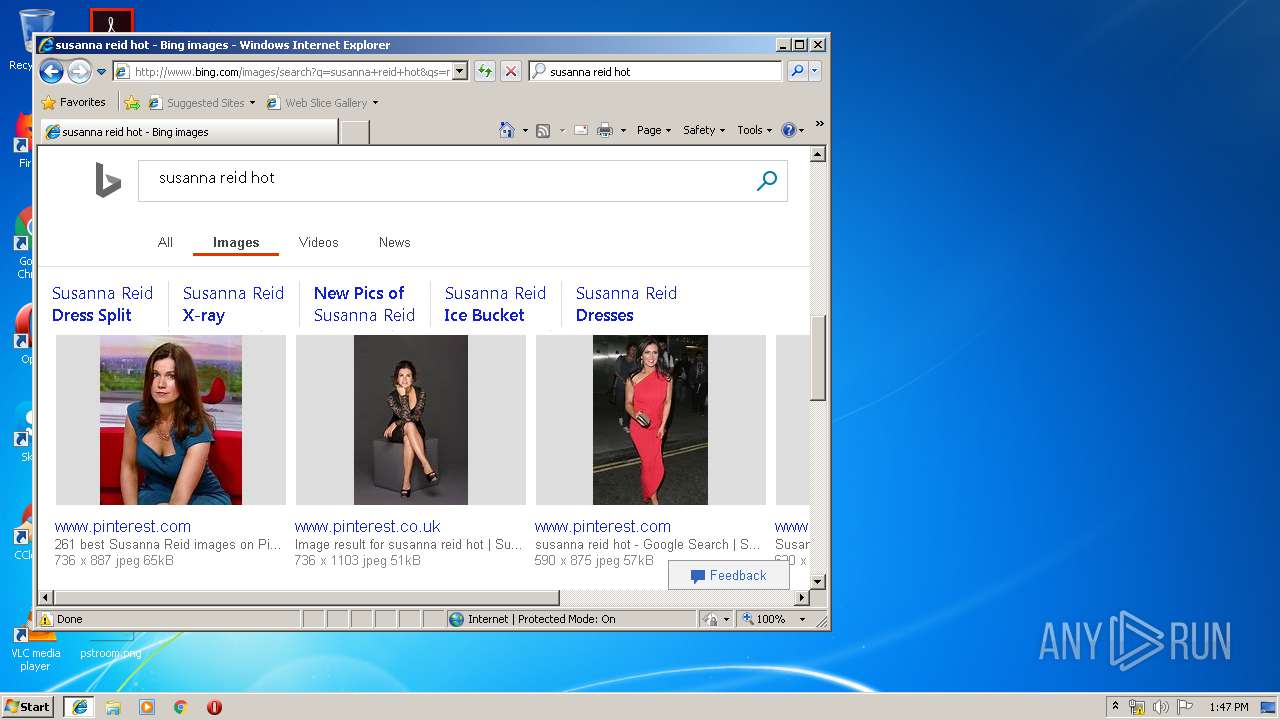
Malware analysis 009E9015BDEF9F869B5F15A526D9A1B1 Malicious activity
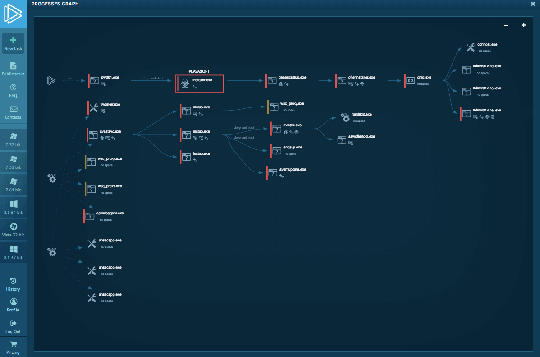
Interactive Online Malware Sandbox

Malware Analysis: Steps & Examples - CrowdStrike
Malware analysis index.html Malicious activity

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware Analysis Framework v1.0

Dynamic Malware Analysis in the Modern Era—A State of the Art Survey

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

How to build a malware analysis sandbox with Elastic Security
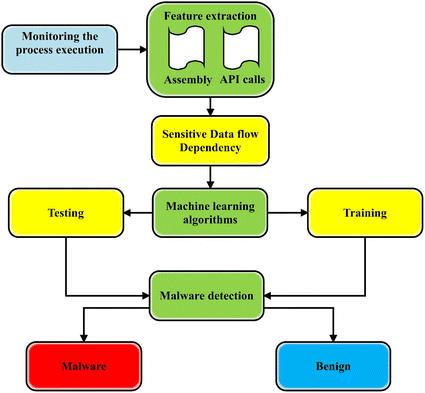
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences
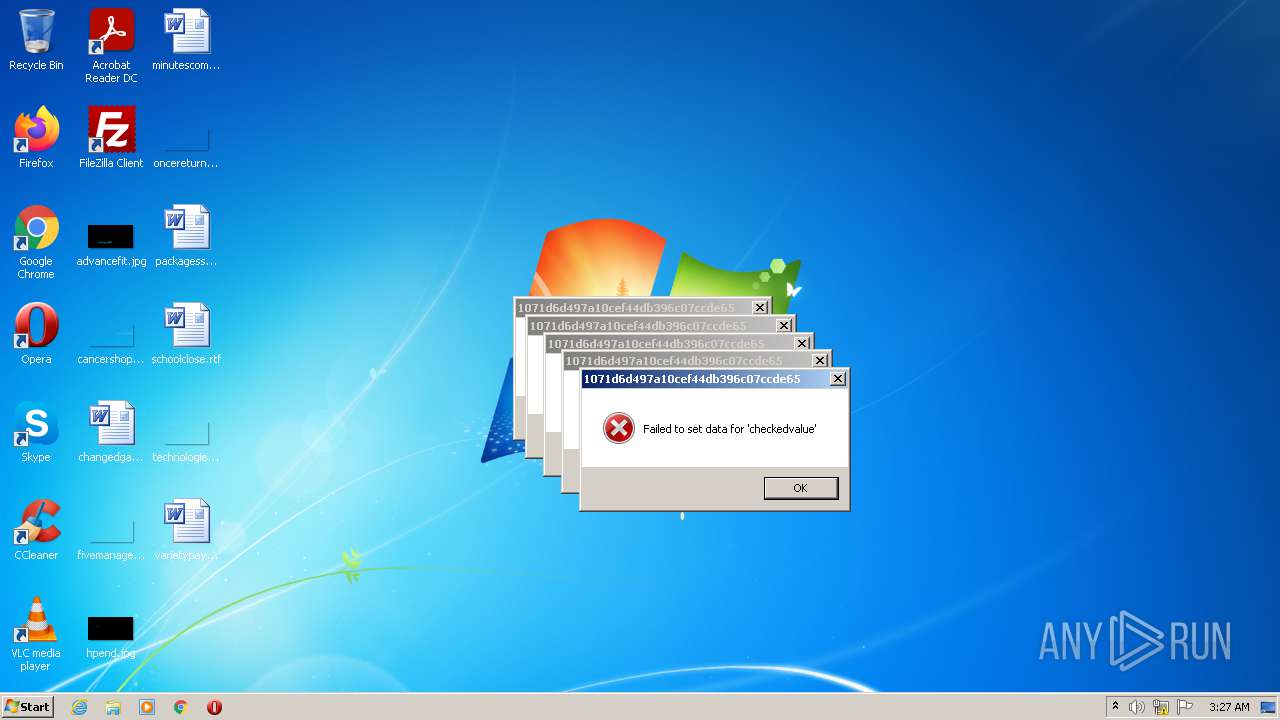
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity
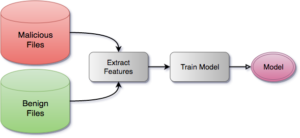
Detecting Malware Pre-execution with Static Analysis and Machine Learning - SentinelOne
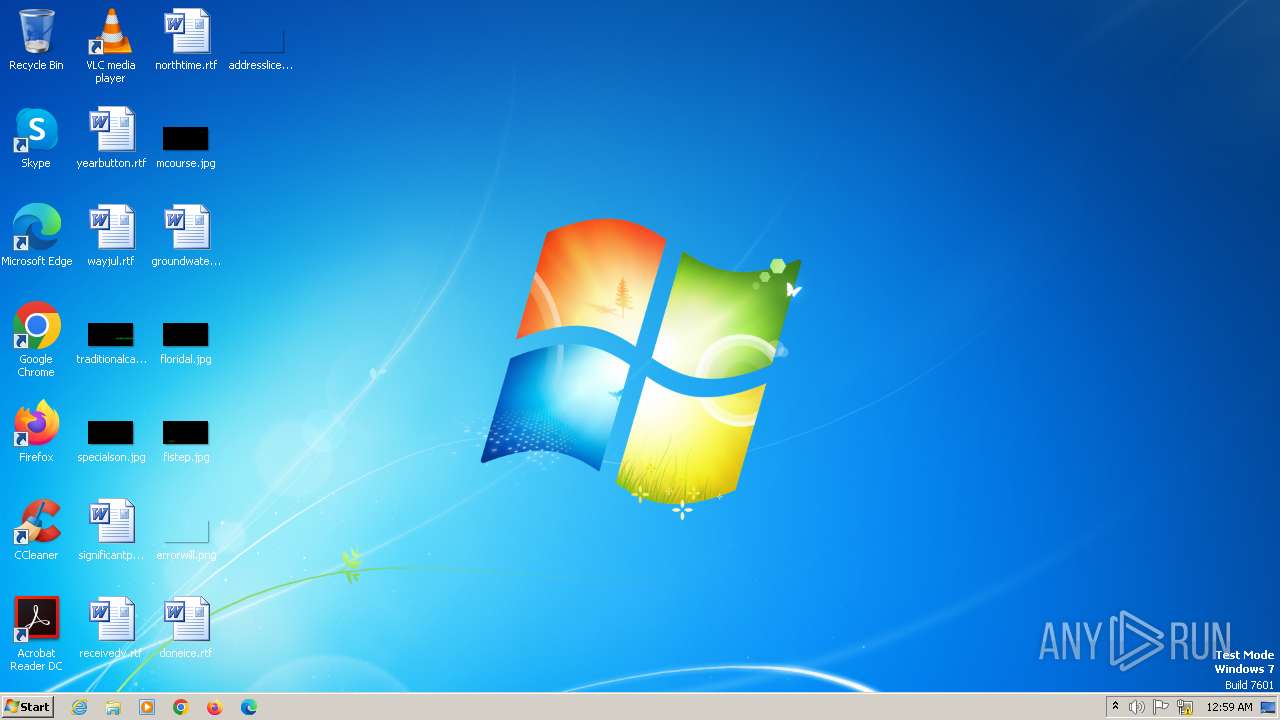
Malware analysis file Malicious activity
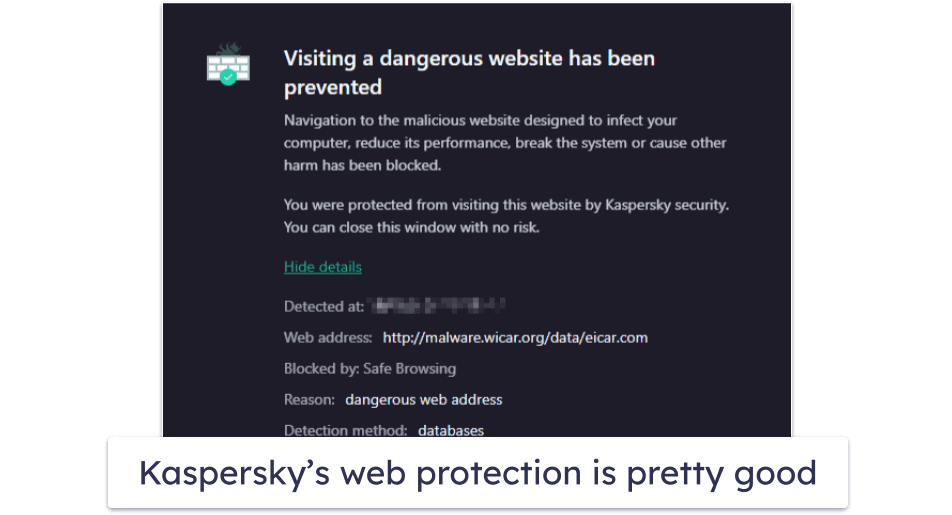
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
Recomendado para você
-
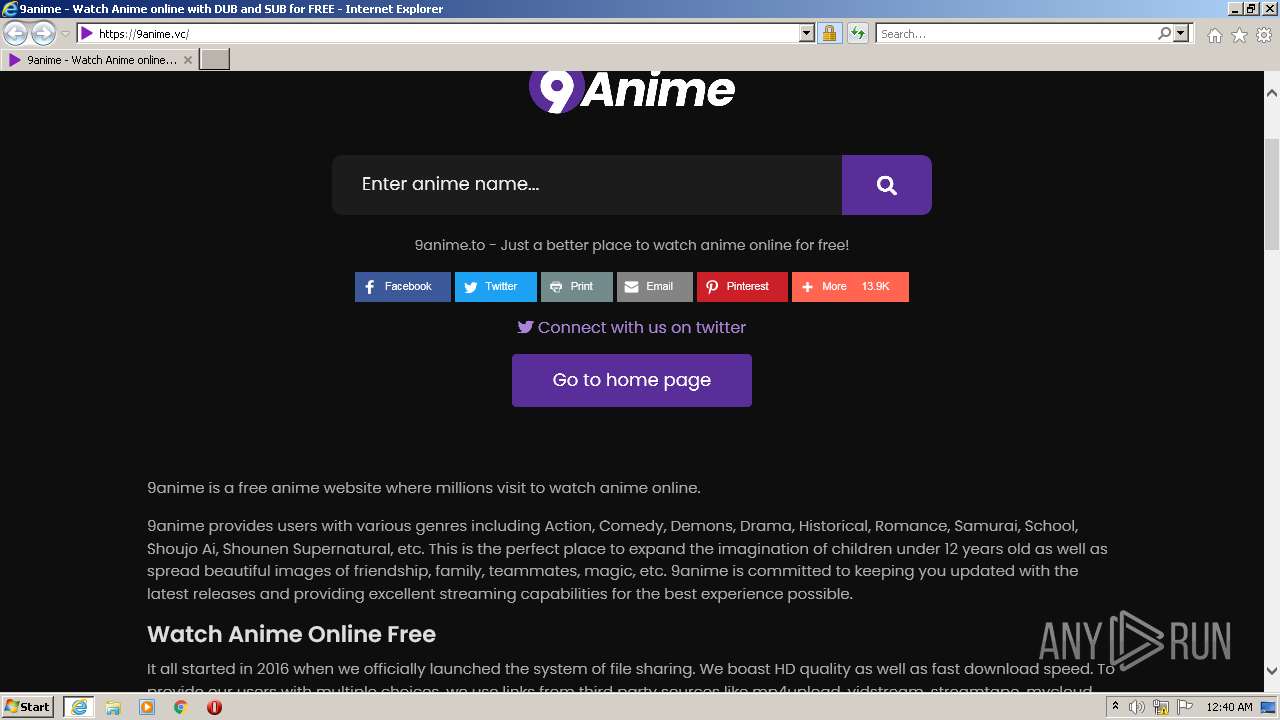
 9anime - Watch Free Anime Online02 abril 2025
9anime - Watch Free Anime Online02 abril 2025 -
 9anime.id é confiável? 9anime é segura?02 abril 2025
9anime.id é confiável? 9anime é segura?02 abril 2025 -
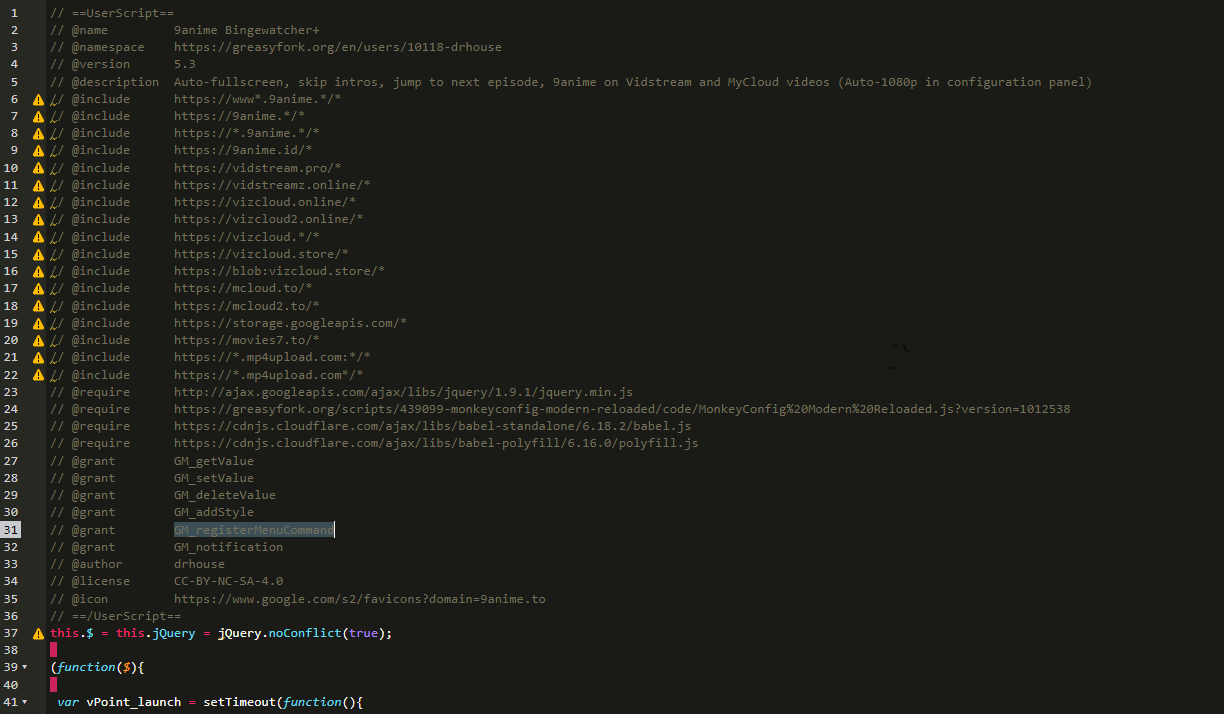 9anime) AniWave Bingewatcher+ - Feedback02 abril 2025
9anime) AniWave Bingewatcher+ - Feedback02 abril 2025 -
Anime Beach Tramandaí RS02 abril 2025
-
 BOMBA! SENTAI vai Lançar ANIMES do HIDIVE na NETFLIX e STAR PLUS no BRASIL!02 abril 2025
BOMBA! SENTAI vai Lançar ANIMES do HIDIVE na NETFLIX e STAR PLUS no BRASIL!02 abril 2025 -
Download 9anime - TruePremium on PC (Emulator) - LDPlayer02 abril 2025
-
Esesadu Baaga esesadu Anime: Demon Slayer: Swordsmith Village #hades Check out our Discord and Telegram (Link in Bio) . . . . . #anime…02 abril 2025
-
Steam Workshop::Black Clover Opening 9 Anime02 abril 2025
-
Anime Movie Run Melos Special English Dubbed - video Dailymotion02 abril 2025
-
 Fire Emblem Heroes 1'' Eliwood Acrylic Stand Figure Vol. 9 Anime Manga NEW02 abril 2025
Fire Emblem Heroes 1'' Eliwood Acrylic Stand Figure Vol. 9 Anime Manga NEW02 abril 2025
você pode gostar
-
 Roma's Henrikh Mkhitaryan is making a case as the best midfielder in Europe – Public Radio of Armenia02 abril 2025
Roma's Henrikh Mkhitaryan is making a case as the best midfielder in Europe – Public Radio of Armenia02 abril 2025 -
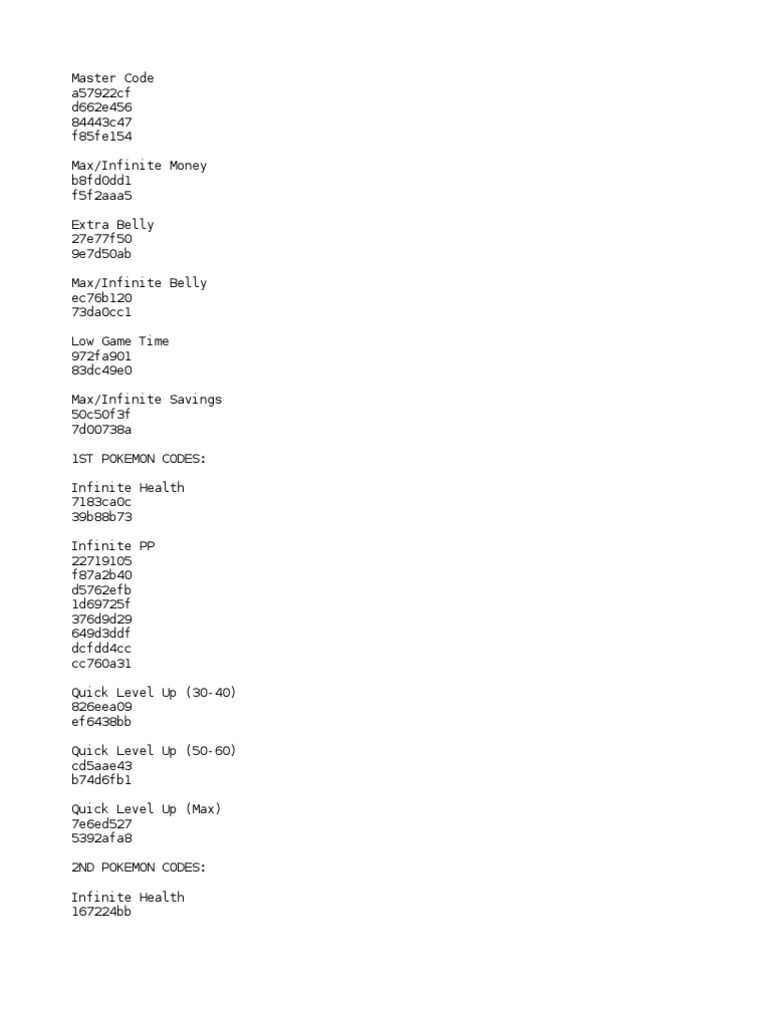
Pokemon Mystery Dungeon Red Rescue Team Gameshark Code02 abril 2025
-
 Fundo Coelhinho Fofo Em Flores Cor De Rosa Com Um Laço Em Volta Da02 abril 2025
Fundo Coelhinho Fofo Em Flores Cor De Rosa Com Um Laço Em Volta Da02 abril 2025 -
 Sarja Estampada Impermeável Xadrez Moderno Colorido Azul02 abril 2025
Sarja Estampada Impermeável Xadrez Moderno Colorido Azul02 abril 2025 -
 Gameloop Mobi, a imitação do site oficial da Gameloop02 abril 2025
Gameloop Mobi, a imitação do site oficial da Gameloop02 abril 2025 -
 Epic Games Store : vous n'êtes pas prêts, le jeu gratuit de la semaine va griller vos méninges02 abril 2025
Epic Games Store : vous n'êtes pas prêts, le jeu gratuit de la semaine va griller vos méninges02 abril 2025 -
 Mundo dos Super-Heróis Edicao 136 (Digital)02 abril 2025
Mundo dos Super-Heróis Edicao 136 (Digital)02 abril 2025 -
 BUDAPEST, HUNGARY - APRIL 2: Krisztian Lisztes of Ferencvarosi TC celebrates with teammates after scoring a goal during the Hungarian OTP Bank Liga match between Ferencvarosi TC and MOL Fehervar FC at02 abril 2025
BUDAPEST, HUNGARY - APRIL 2: Krisztian Lisztes of Ferencvarosi TC celebrates with teammates after scoring a goal during the Hungarian OTP Bank Liga match between Ferencvarosi TC and MOL Fehervar FC at02 abril 2025 -
 Thor's Tattoos Leaked!! (God of War Theory)02 abril 2025
Thor's Tattoos Leaked!! (God of War Theory)02 abril 2025 -
 QUIZ YUTUBERS ESPERO QUE GOSTEM02 abril 2025
QUIZ YUTUBERS ESPERO QUE GOSTEM02 abril 2025