Malware analysis Malicious activity
Por um escritor misterioso
Last updated 03 março 2025

Malware Analysis: Steps & Examples - CrowdStrike
Interactive Online Malware Sandbox

How to Analyze Malware's Network Traffic in A Sandbox

TryHackMe Cyber Security Exercises and Labs

Endpoint Detection and Response, Free - What is EDR Security?

Robust Malware Detection Models: Learning From Adversarial Attacks

MetaDefender Cloud Advanced threat prevention and detection

Feature Extraction and Detection of Malwares Using Machine

Malware analysis Program_Install_and_Uninstall Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?

TryHackMe Hacktivities

The Guide to Ransomware Solutions in 2023 - Security Boulevard

An Elastic approach to large-scale dynamic malware analysis
Recomendado para você
-
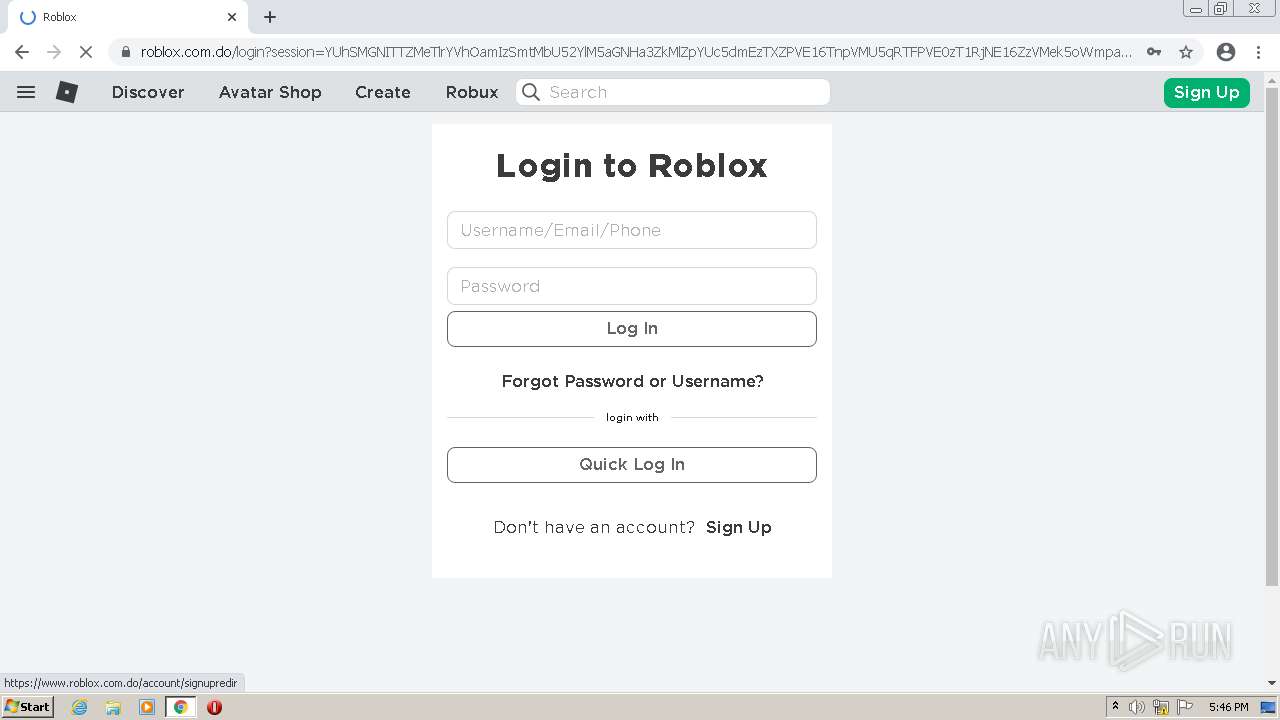
 Roblox Games Login www.roblox.com03 março 2025
Roblox Games Login www.roblox.com03 março 2025 -
www.roblox.com - see bug description · Issue #45398 · webcompat/web-bugs · GitHub03 março 2025
-
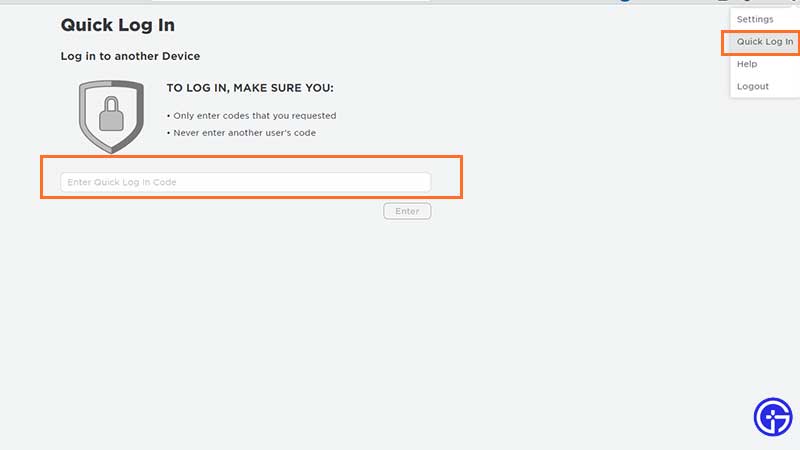 How To Use Roblox Quick Login Feature (2023) - Gamer Tweak03 março 2025
How To Use Roblox Quick Login Feature (2023) - Gamer Tweak03 março 2025 -
 How to View Purchase History in Roblox03 março 2025
How to View Purchase History in Roblox03 março 2025 -
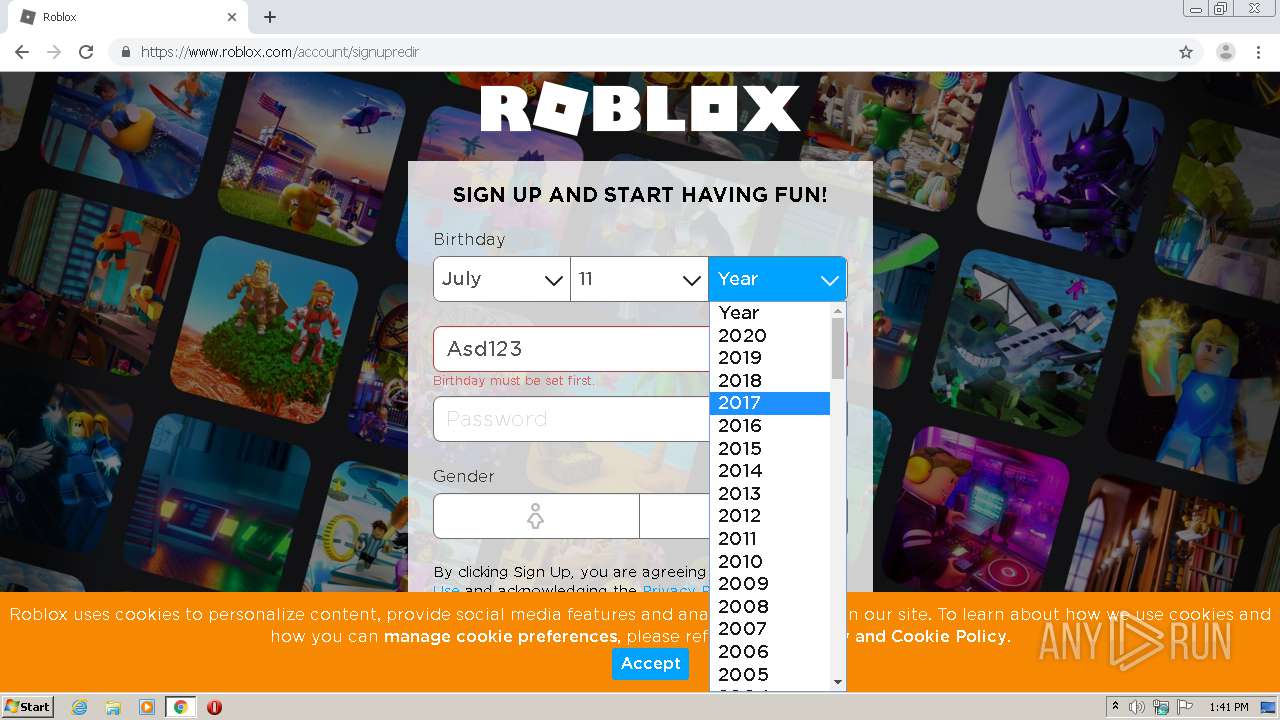
 6 Easy Ways to Install Roblox and Roblox Studio03 março 2025
6 Easy Ways to Install Roblox and Roblox Studio03 março 2025 -
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2020/x/S/DyH4pBSK6fiDnBBWg5Tg/roblox-como-criar-mapa-passo-5-templates.jpg) Como criar, publicar e editar um mapa no Roblox03 março 2025
Como criar, publicar e editar um mapa no Roblox03 março 2025 -
 Malware analysis Malicious activity03 março 2025
Malware analysis Malicious activity03 março 2025 -
 Roblox-free-game-websites - Probytes Web Development Company03 março 2025
Roblox-free-game-websites - Probytes Web Development Company03 março 2025 -
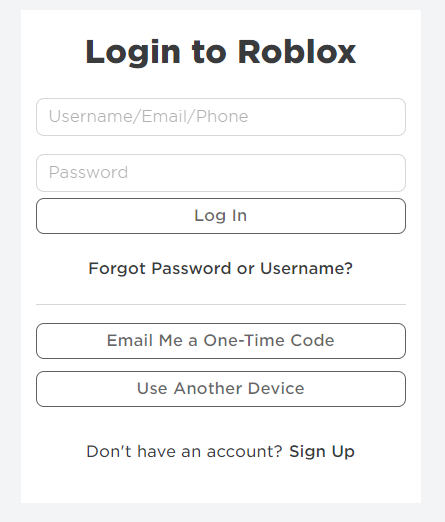 Introducing Login with a One-Time Code - Announcements - Developer Forum03 março 2025
Introducing Login with a One-Time Code - Announcements - Developer Forum03 março 2025 -
Play Roblox Online for Free on PC & Mobile03 março 2025
você pode gostar
-
 Depeche Mode y Kendrick Lamar resucitan con sus grandes03 março 2025
Depeche Mode y Kendrick Lamar resucitan con sus grandes03 março 2025 -
 Machine Doll Unbreakable machine doll, Anime, Manga03 março 2025
Machine Doll Unbreakable machine doll, Anime, Manga03 março 2025 -
 So when is Kingambit getting added into PoGo? still can't believe i got this shiny. : r/pokemongo03 março 2025
So when is Kingambit getting added into PoGo? still can't believe i got this shiny. : r/pokemongo03 março 2025 -
 Infinite Dendrogram Light Novel Review03 março 2025
Infinite Dendrogram Light Novel Review03 março 2025 -
 nomes femininos personalizados para free fire03 março 2025
nomes femininos personalizados para free fire03 março 2025 -
 Yippee maker|Picrew03 março 2025
Yippee maker|Picrew03 março 2025 -
 Inkspired - Abunai Aisuru03 março 2025
Inkspired - Abunai Aisuru03 março 2025 -
 Jogo Quebra Cabeça 3D Dinossauros em MDF (Uriarte)03 março 2025
Jogo Quebra Cabeça 3D Dinossauros em MDF (Uriarte)03 março 2025 -
 Clássico metal fio mágico jogo de quebra-cabeça para jovens e idosos - AliExpress03 março 2025
Clássico metal fio mágico jogo de quebra-cabeça para jovens e idosos - AliExpress03 março 2025 -
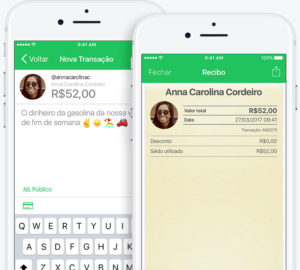 Pic pay é Seguro e Confiável? Como Receber Sem Máquina de Cartão?03 março 2025
Pic pay é Seguro e Confiável? Como Receber Sem Máquina de Cartão?03 março 2025