Malware analysis Malicious
Por um escritor misterioso
Last updated 10 março 2025

PDF] A Survey on Malware Detection and Analysis Tools

The Top 10 Malware Analysis Tools

Malware Analysis Tips and Tricks.pdf

Malware Analysis: Protecting Your Network from Cyber Attacks
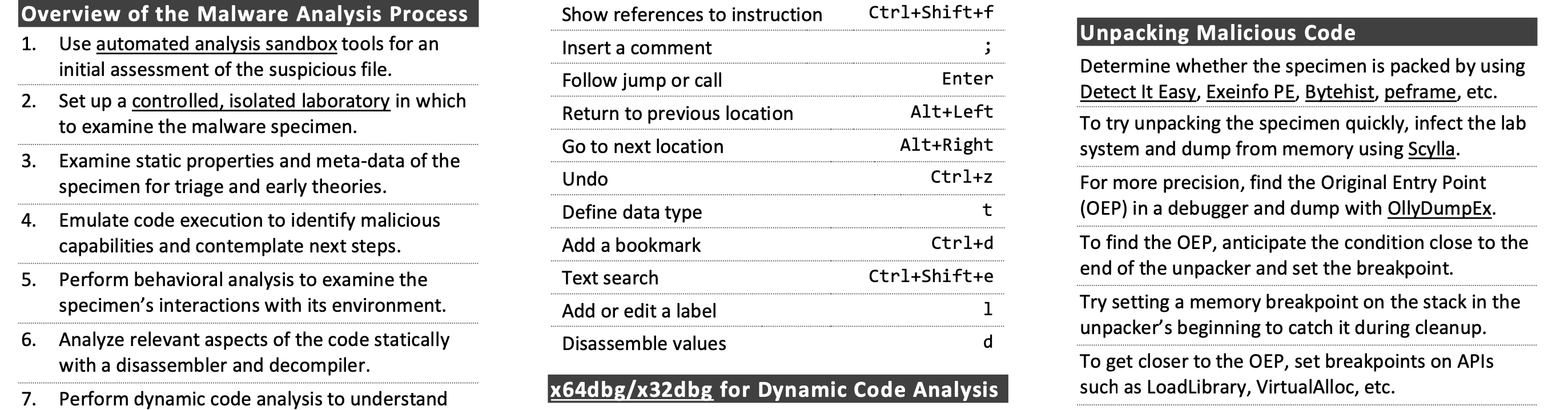
Cheat Sheet for Analyzing Malicious Software
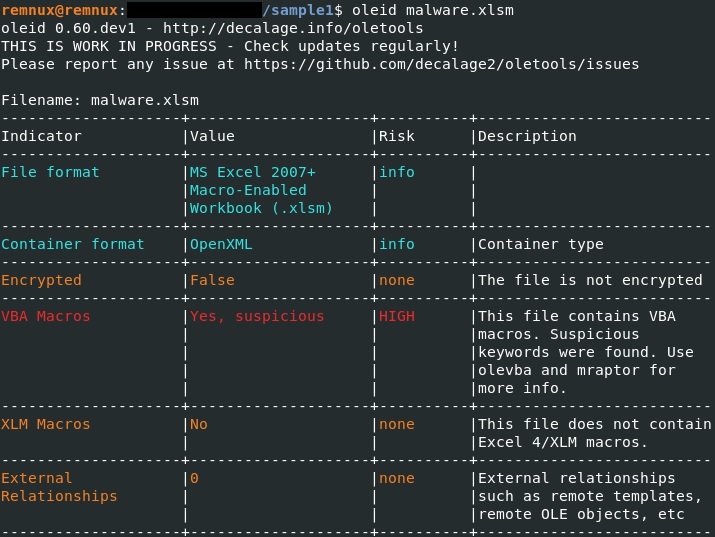
How to analyze malicious documents – Case study of an attack targeting Ukrainian Organizations – CYBER GEEKS

How to Do Malware Analysis?
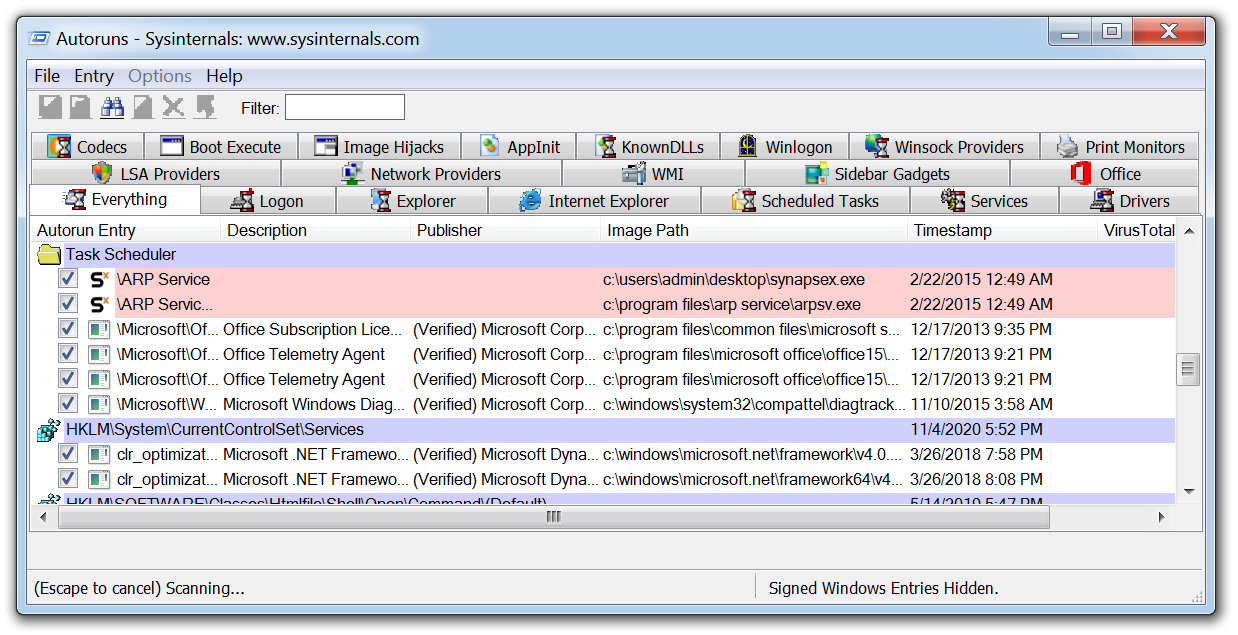
11 Best Malware Analysis Tools and Their Features
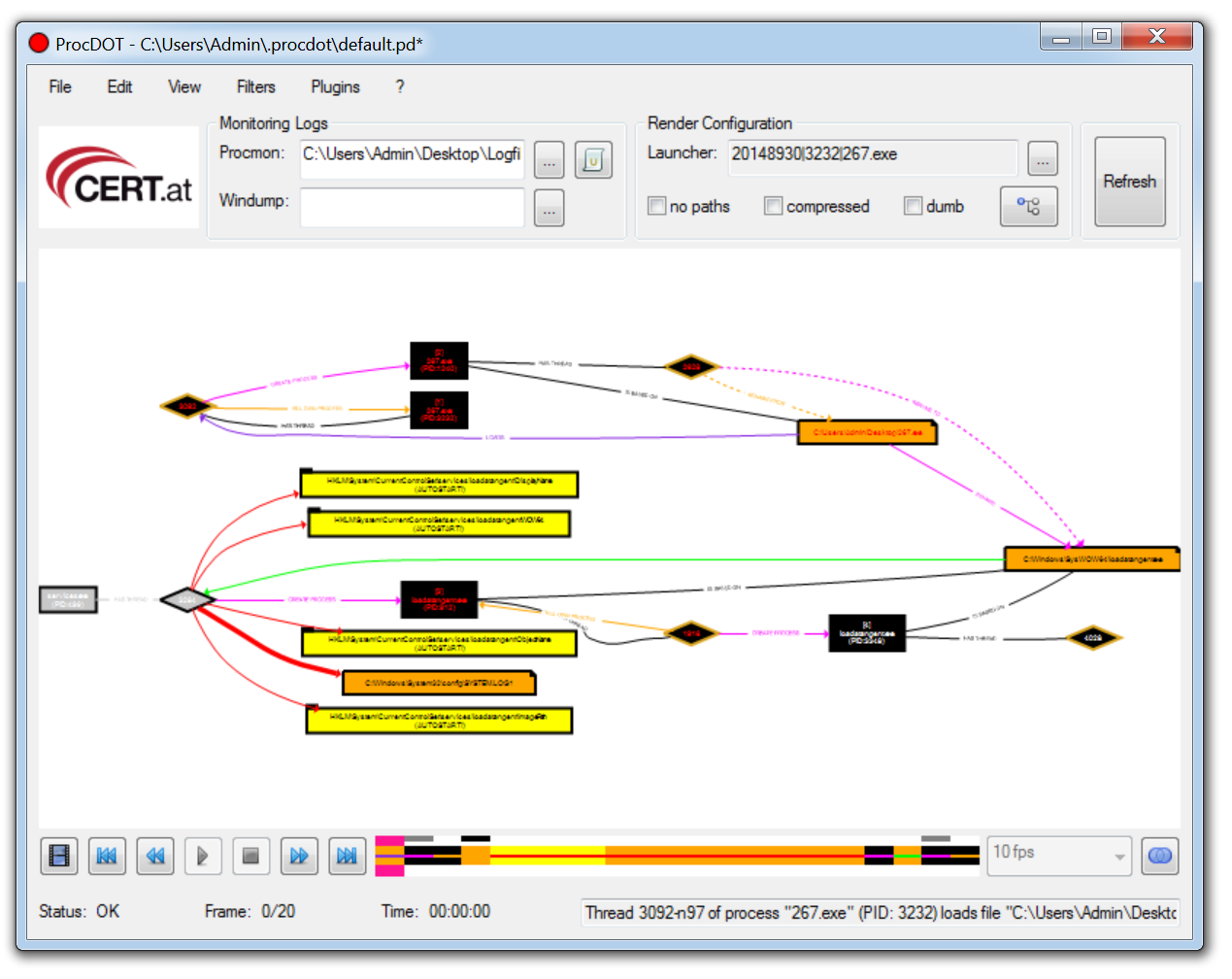
11 Best Malware Analysis Tools and Their Features

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
Recomendado para você
-
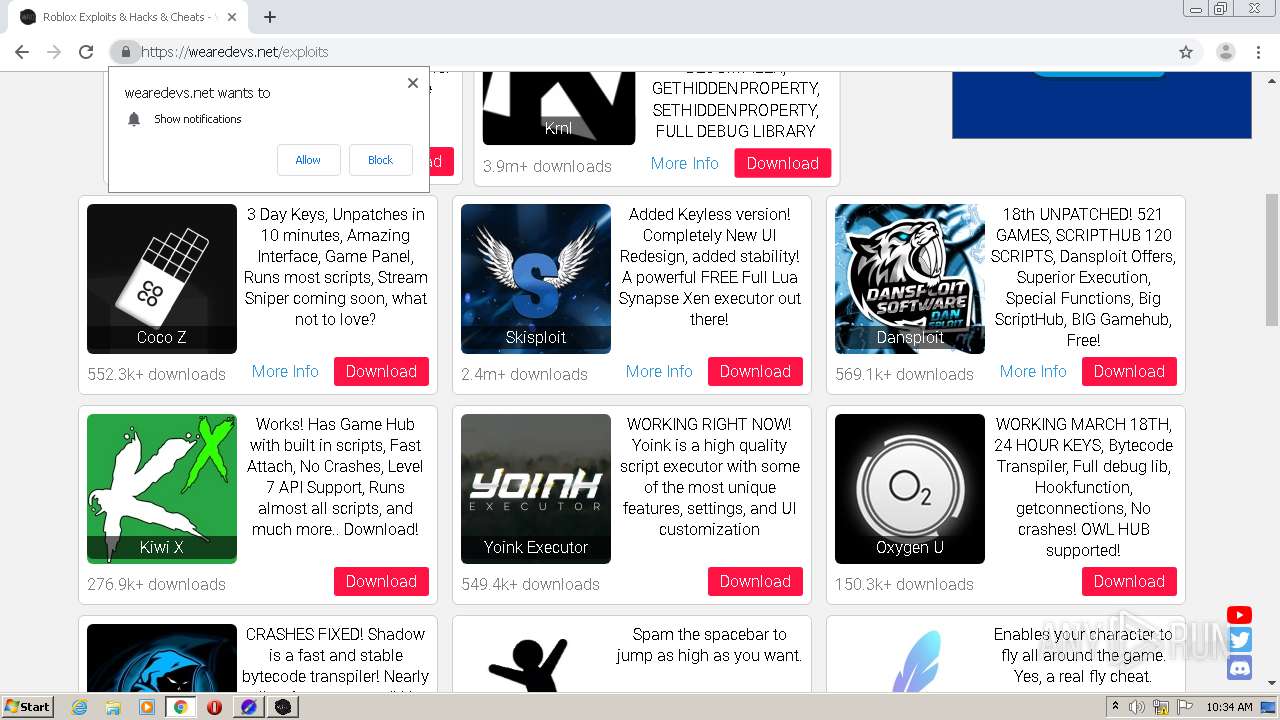
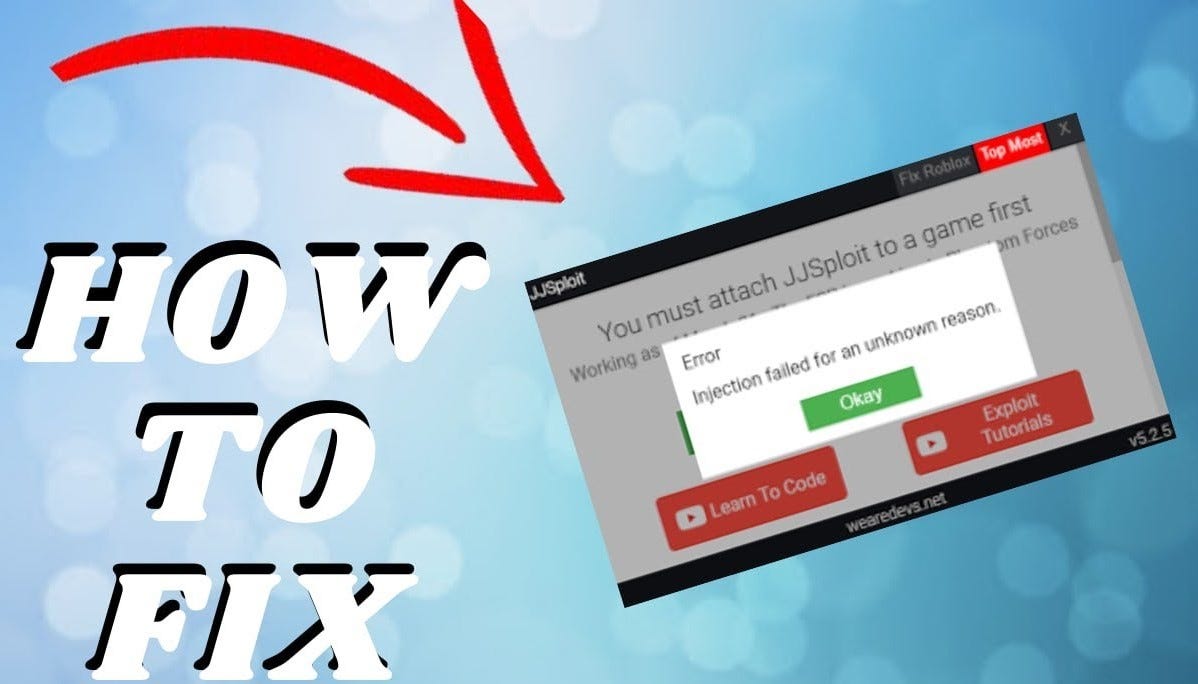 How To Fix Your JJSploit Not Injecting?, by Jjsploit10 março 2025
How To Fix Your JJSploit Not Injecting?, by Jjsploit10 março 2025 -
wearedevs.net Competitors - Top Sites Like wearedevs.net10 março 2025
-
 Neuron, Strong Level 6/7 FREE Exploit, Executes most scripts, Multi API ( WeAreDevs, Bloxsploits, Axon)10 março 2025
Neuron, Strong Level 6/7 FREE Exploit, Executes most scripts, Multi API ( WeAreDevs, Bloxsploits, Axon)10 março 2025 -
Replying to @eli tut on how to install fluxus10 março 2025
-
![PATCHED] ROBLOX SCRIPTS ( SYNAPSE CRACKEADO ) - Outros Jogos Battle Royale - WebCheats](https://user-images.githubusercontent.com/113463089/191644913-5e37fea8-c0a8-4f4e-90bb-4492aee41623.png) PATCHED] ROBLOX SCRIPTS ( SYNAPSE CRACKEADO ) - Outros Jogos Battle Royale - WebCheats10 março 2025
PATCHED] ROBLOX SCRIPTS ( SYNAPSE CRACKEADO ) - Outros Jogos Battle Royale - WebCheats10 março 2025 -
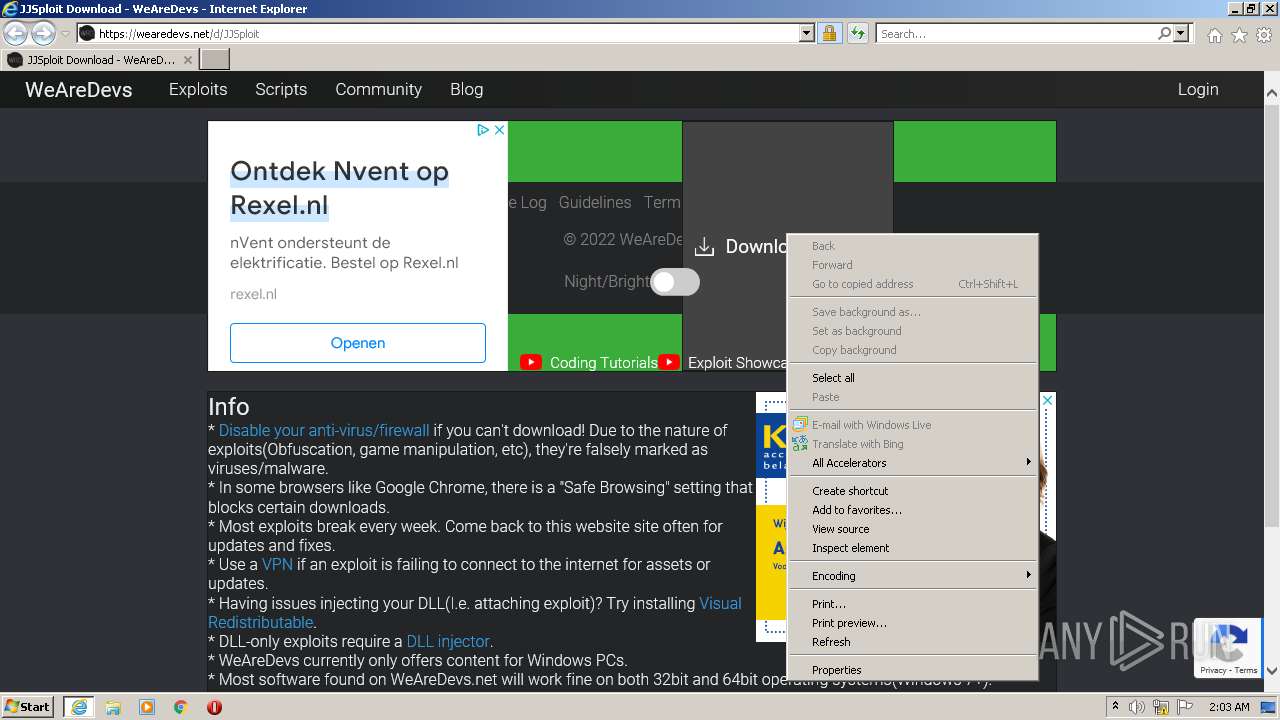
 WeAreDevs API is Faulty! - WRD Community10 março 2025
WeAreDevs API is Faulty! - WRD Community10 março 2025 -
teri eyenike en LinkedIn: I will be giving a session on how to use10 março 2025
-
 roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment “tuto10 março 2025
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment “tuto10 março 2025 -
 Malware analysis Malicious10 março 2025
Malware analysis Malicious10 março 2025 -
 How To Create A Roblox Exploit, Full Featured Template10 março 2025
How To Create A Roblox Exploit, Full Featured Template10 março 2025
você pode gostar
-
 Assistir Kimetsu no Yaiba: Mugen Ressha-hen Dublado Todos os Episódios Online10 março 2025
Assistir Kimetsu no Yaiba: Mugen Ressha-hen Dublado Todos os Episódios Online10 março 2025 -
 Facebook and Google Login, Register by Bonpresta10 março 2025
Facebook and Google Login, Register by Bonpresta10 março 2025 -
 Download Snack Video - Funny videos APK10 março 2025
Download Snack Video - Funny videos APK10 março 2025 -
 Ranking The Top 15 Best Players In The NBA Right Now - Fadeaway World10 março 2025
Ranking The Top 15 Best Players In The NBA Right Now - Fadeaway World10 março 2025 -
 Dragon Ball FighterZ pode não ter dublagem e isso não faz nenhum sentido - 05/10/2017 - UOL Start10 março 2025
Dragon Ball FighterZ pode não ter dublagem e isso não faz nenhum sentido - 05/10/2017 - UOL Start10 março 2025 -
 The Legend of Zelda: The Wind Waker - GameCube (NGC) ROM - Download10 março 2025
The Legend of Zelda: The Wind Waker - GameCube (NGC) ROM - Download10 março 2025 -
 John Carpenter's Suburban Screams A Killer Comes Home (TV Episode 2023) - IMDb10 março 2025
John Carpenter's Suburban Screams A Killer Comes Home (TV Episode 2023) - IMDb10 março 2025 -
 The Sims Freeplay- Beginners Guide – The Girl Who Games10 março 2025
The Sims Freeplay- Beginners Guide – The Girl Who Games10 março 2025 -
 Crítica de Frozen 210 março 2025
Crítica de Frozen 210 março 2025 -
 How boosting works in League of Legends - Eloking10 março 2025
How boosting works in League of Legends - Eloking10 março 2025

