Jump Host Best Practices — Improsec
Por um escritor misterioso
Last updated 20 novembro 2024

Because a jump host serves at an entry point to privileged resources it is a highly sought target by adversaries. Therefore, it is important to have an increased focus on security. However hardening the jump host itself it not enough, a holistic approach is needed. In this blog, Jakob provides solid
Publishing Updates

Next Generation Jump Servers for Industrial Control Systems - PDF
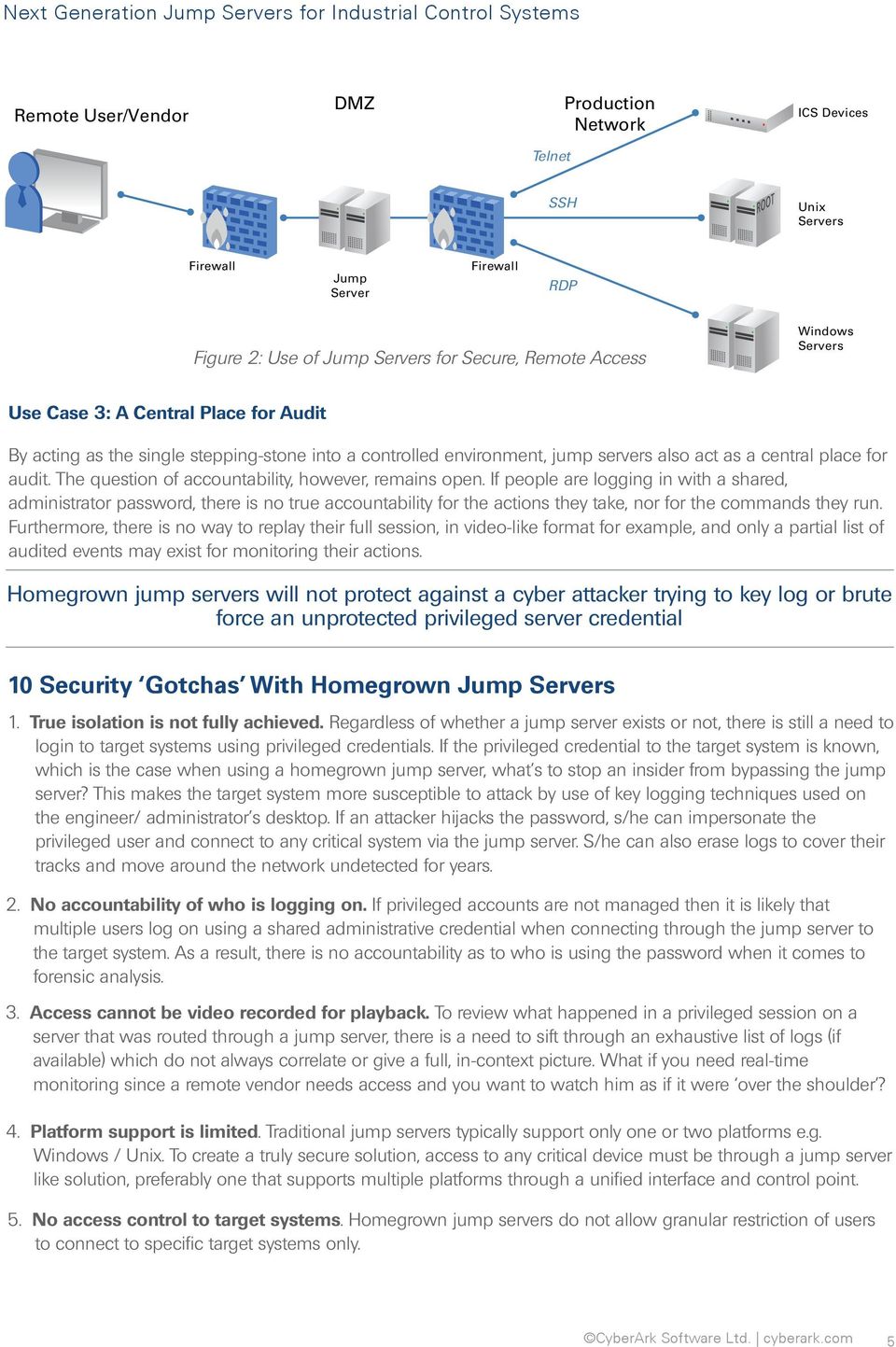
Next Generation Jump Servers for Industrial Control Systems - PDF
GitHub - taielab/awesome-hacking-lists: 平常看到好的渗透hacking

MITRE ATT&CK Updates: State of the ATT&CK (ATT&CKcon 4.0 Edition
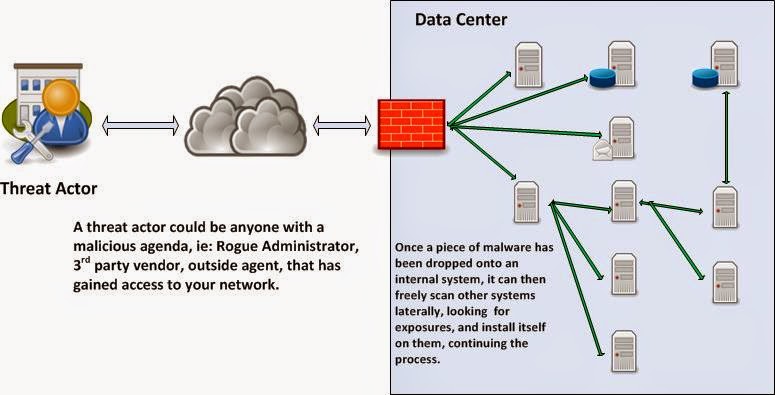
InfoSec Musings: Risk reduction through Jump Servers

What is a Jump Server - Javatpoint

State of the ATT&CK
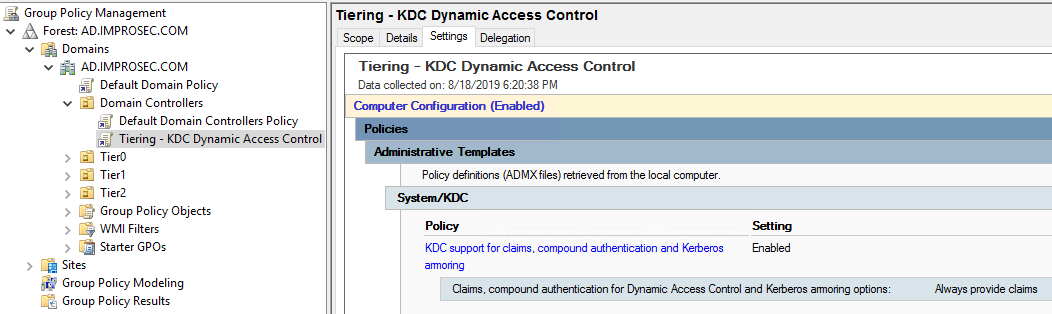
Preventing lateral movement in AD with Authentication Policies
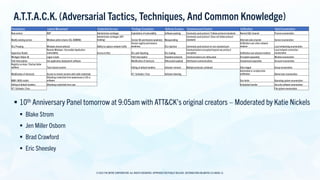
MITRE ATT&CK Updates: State of the ATT&CK (ATT&CKcon 4.0 Edition
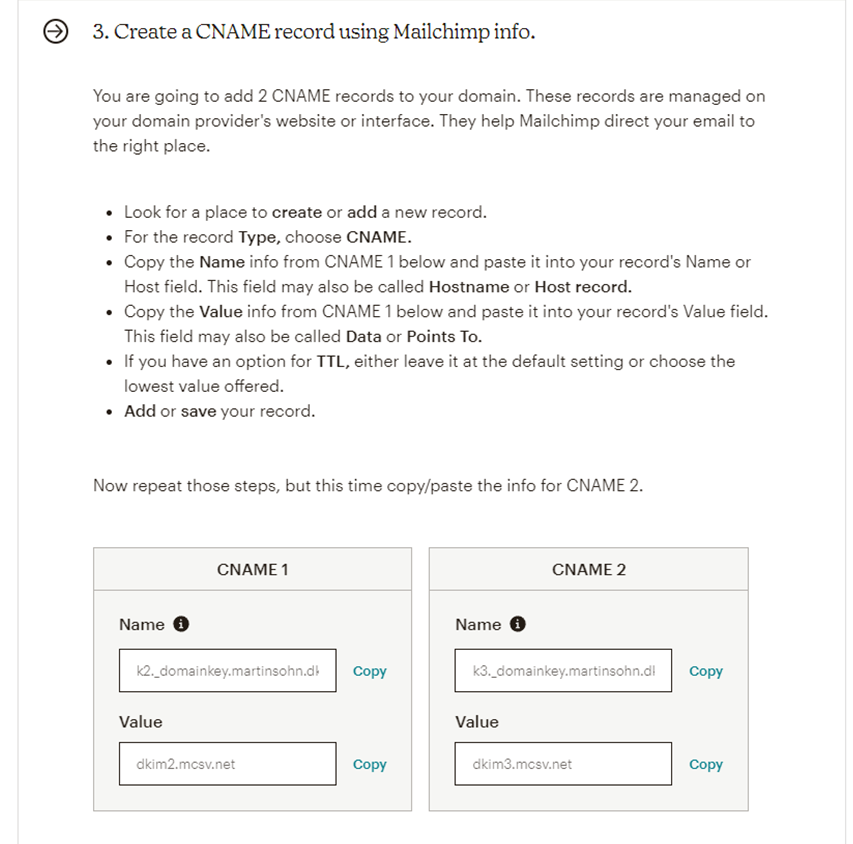
Phish'n'Chimps: mail spoofing via marketing and CRM platforms
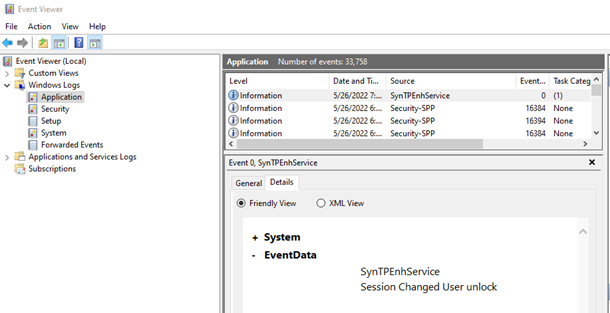
Windows Event Logs for Red Teams - Black Hills Information Security
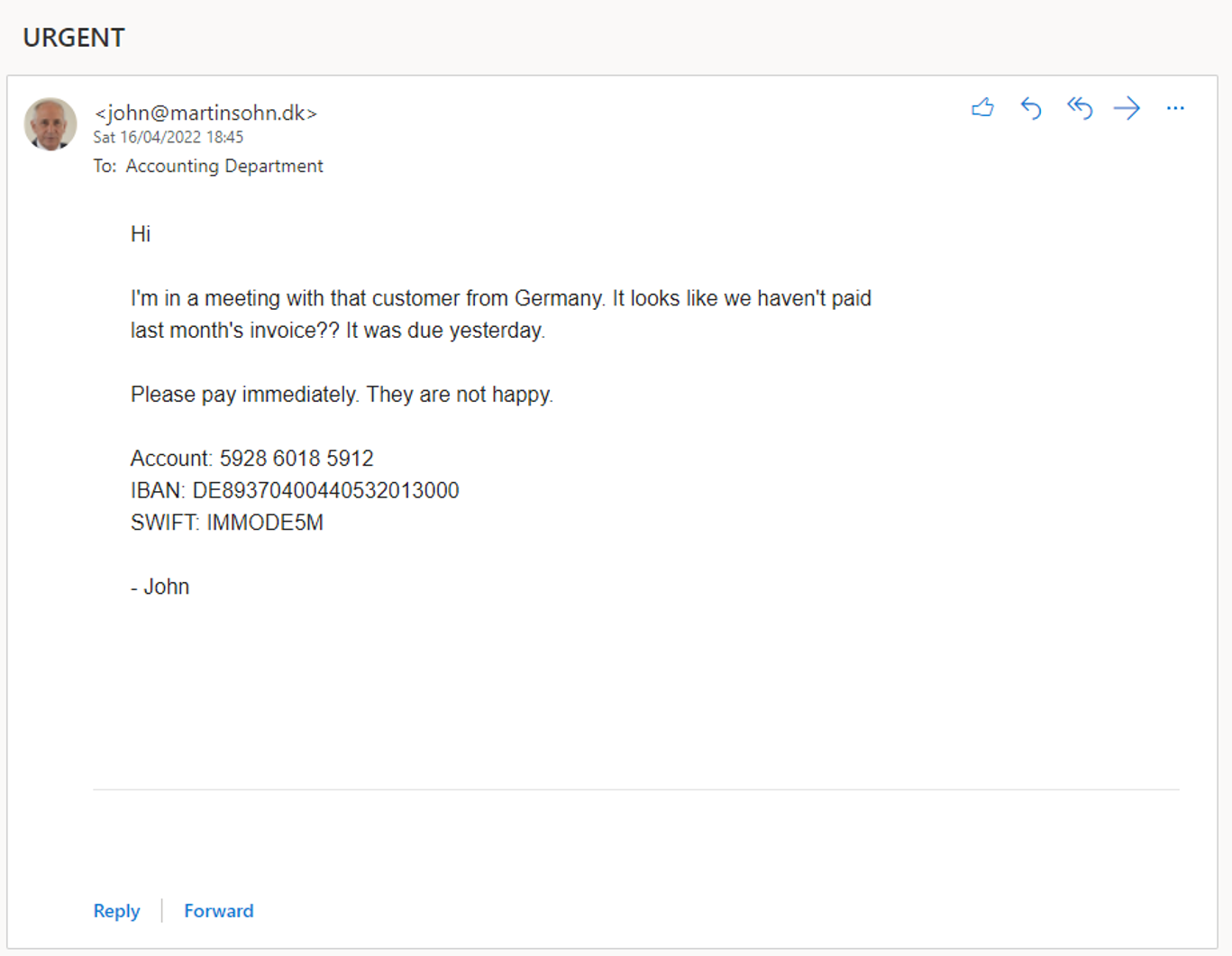
Phish'n'Chimps: mail spoofing via marketing and CRM platforms
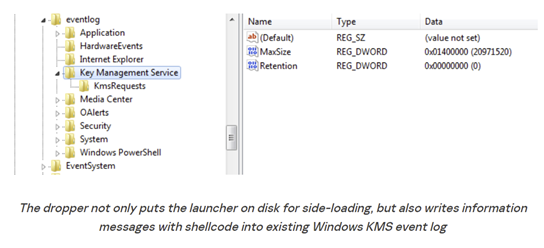
Windows Event Logs for Red Teams - Black Hills Information Security
Recomendado para você
-
 2-in-1 Musical Jump 'n Toss20 novembro 2024
2-in-1 Musical Jump 'n Toss20 novembro 2024 -
 Children are at a high risk of injury when they jump on trampolines.20 novembro 2024
Children are at a high risk of injury when they jump on trampolines.20 novembro 2024 -
 100+ Jump Pictures Download Free Images on Unsplash20 novembro 2024
100+ Jump Pictures Download Free Images on Unsplash20 novembro 2024 -
 Mini Jump Trampolim 32 Molas Profissional para Treino de Musculação em Academia20 novembro 2024
Mini Jump Trampolim 32 Molas Profissional para Treino de Musculação em Academia20 novembro 2024 -
 High Jump20 novembro 2024
High Jump20 novembro 2024 -
 What makes the perfect…long jump?20 novembro 2024
What makes the perfect…long jump?20 novembro 2024 -
High jump rules and regulations20 novembro 2024
-
 Everything to Know About the Triple Jump in Track and Field.20 novembro 2024
Everything to Know About the Triple Jump in Track and Field.20 novembro 2024 -
:max_bytes(150000):strip_icc()/JumpRope-56afa8cc3df78cf772c72bdb.jpg) Learn Simple Conjugations for Sauter (to Jump)20 novembro 2024
Learn Simple Conjugations for Sauter (to Jump)20 novembro 2024 -
 10 Exercises to Improve Your Vertical Jump - Spooner Physical Therapy20 novembro 2024
10 Exercises to Improve Your Vertical Jump - Spooner Physical Therapy20 novembro 2024
você pode gostar
-
 Boneca Bebê Reborn Girafinha Panda Acessórios Magazine Luiza20 novembro 2024
Boneca Bebê Reborn Girafinha Panda Acessórios Magazine Luiza20 novembro 2024 -
 Cyan just send this in the discord and he had this in his hotbar anyone know what is that? : r/GrandPieceOnline20 novembro 2024
Cyan just send this in the discord and he had this in his hotbar anyone know what is that? : r/GrandPieceOnline20 novembro 2024 -
 The Championship's 19 dirtiest players including Sheffield United, Watford, Reading, Millwall, Coventry City and Sunderland stars20 novembro 2024
The Championship's 19 dirtiest players including Sheffield United, Watford, Reading, Millwall, Coventry City and Sunderland stars20 novembro 2024 -
 Superman Black Suit Henry Cavill Justice League Snyder Cut 4K20 novembro 2024
Superman Black Suit Henry Cavill Justice League Snyder Cut 4K20 novembro 2024 -
 static.wikia.nocookie.net/leagueoflegends/images/020 novembro 2024
static.wikia.nocookie.net/leagueoflegends/images/020 novembro 2024 -
 /wp-content/uploads/2023/07/ffo-c20 novembro 2024
/wp-content/uploads/2023/07/ffo-c20 novembro 2024 -
 Que horas são - Pedagogia20 novembro 2024
Que horas são - Pedagogia20 novembro 2024 -
 Desenho de flor pintado e colorido por Lili_7 o dia 19 de Março do 201220 novembro 2024
Desenho de flor pintado e colorido por Lili_7 o dia 19 de Março do 201220 novembro 2024 -
 Imóveis Rua Otto Unger Imóveis à venda em Rua Otto Unger Centro Mogi das Cruzes20 novembro 2024
Imóveis Rua Otto Unger Imóveis à venda em Rua Otto Unger Centro Mogi das Cruzes20 novembro 2024 -
 JUMP FORCE MUGEN ANDROID 2022, FULL 230 KARAKTER20 novembro 2024
JUMP FORCE MUGEN ANDROID 2022, FULL 230 KARAKTER20 novembro 2024