Credential Stuffing 2.0: The Use of Proxies, CAPTCHA Bypassing
Por um escritor misterioso
Last updated 06 março 2025
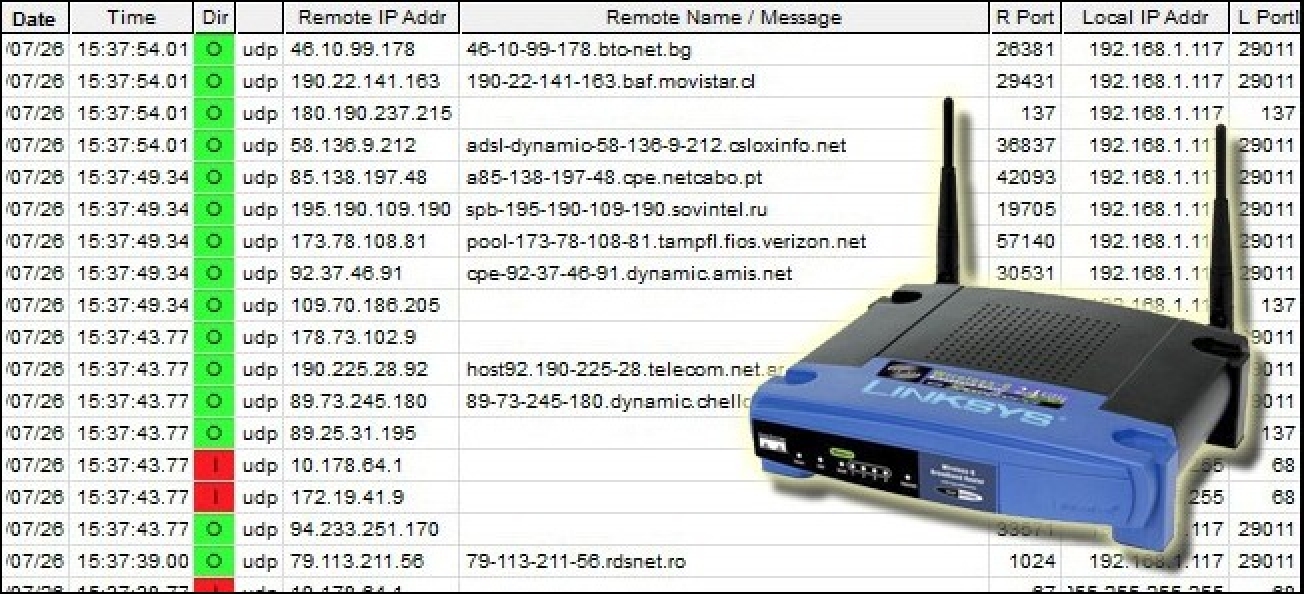
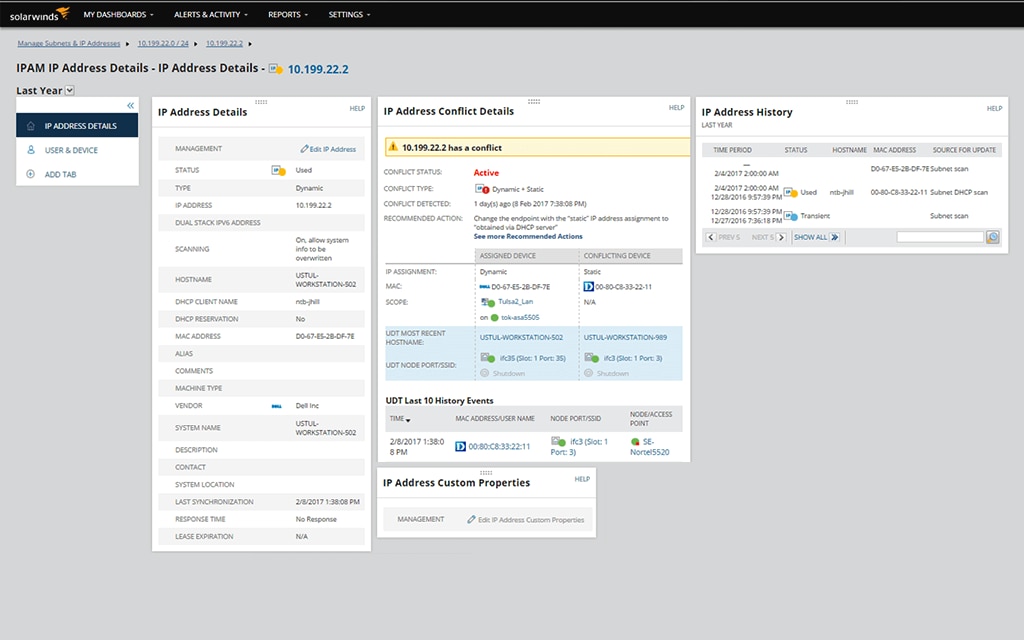
Welcome to the new age of cyber attacks, where hackers have taken credential stuffing to the next level. Meet Credential Stuffing 2.0, where the use of proxies, CAPTCHA bypassing, CloudFlare security, and GUI tools have become the norm..
Credential stuffing simplified + attack protection tips
How to Bypass Cloudflare Bot Protection? Web Scraping Service in 2023

How To Bypass PerimeterX in 2023
The Anatomy of Highly Profitable Credential Stuffing Attacks
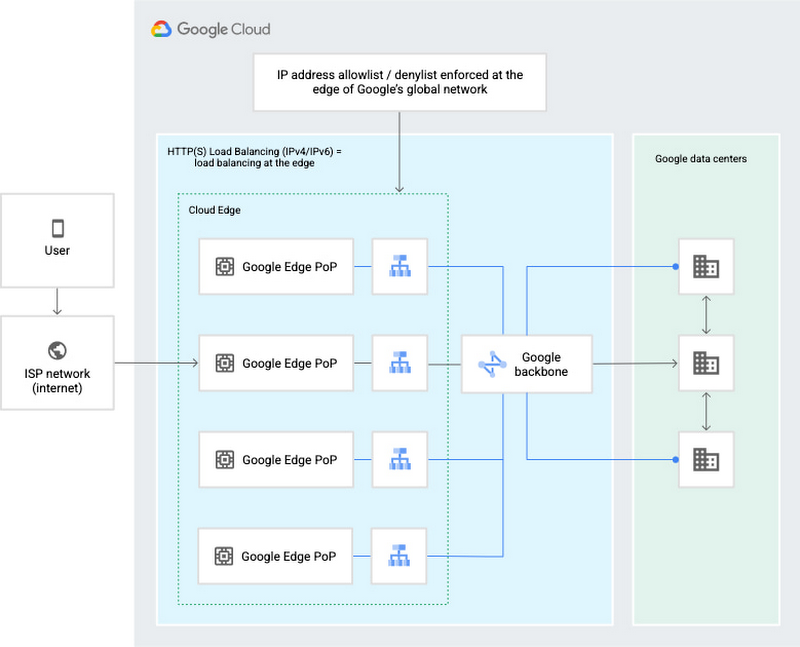
How Google Cloud can help stop credential stuffing attacks
Email Compromise with Credential Stuffing Attack Tools

Email Compromise with Credential Stuffing Attack Tools

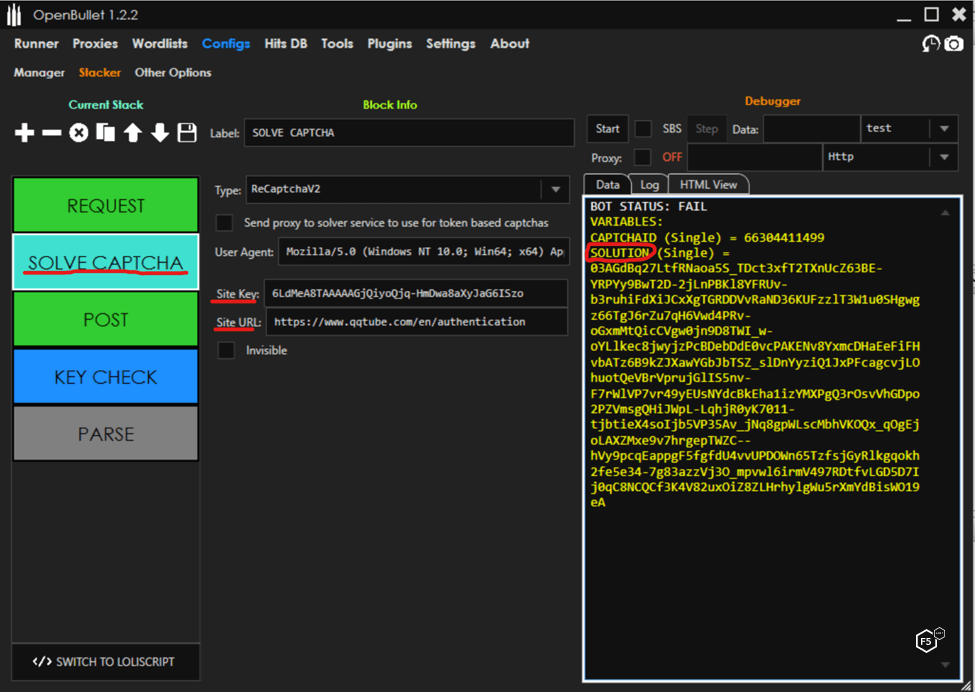
Credential Stuffing Tools and Techniques, Part 1
How To Bypass DataDome in 2023
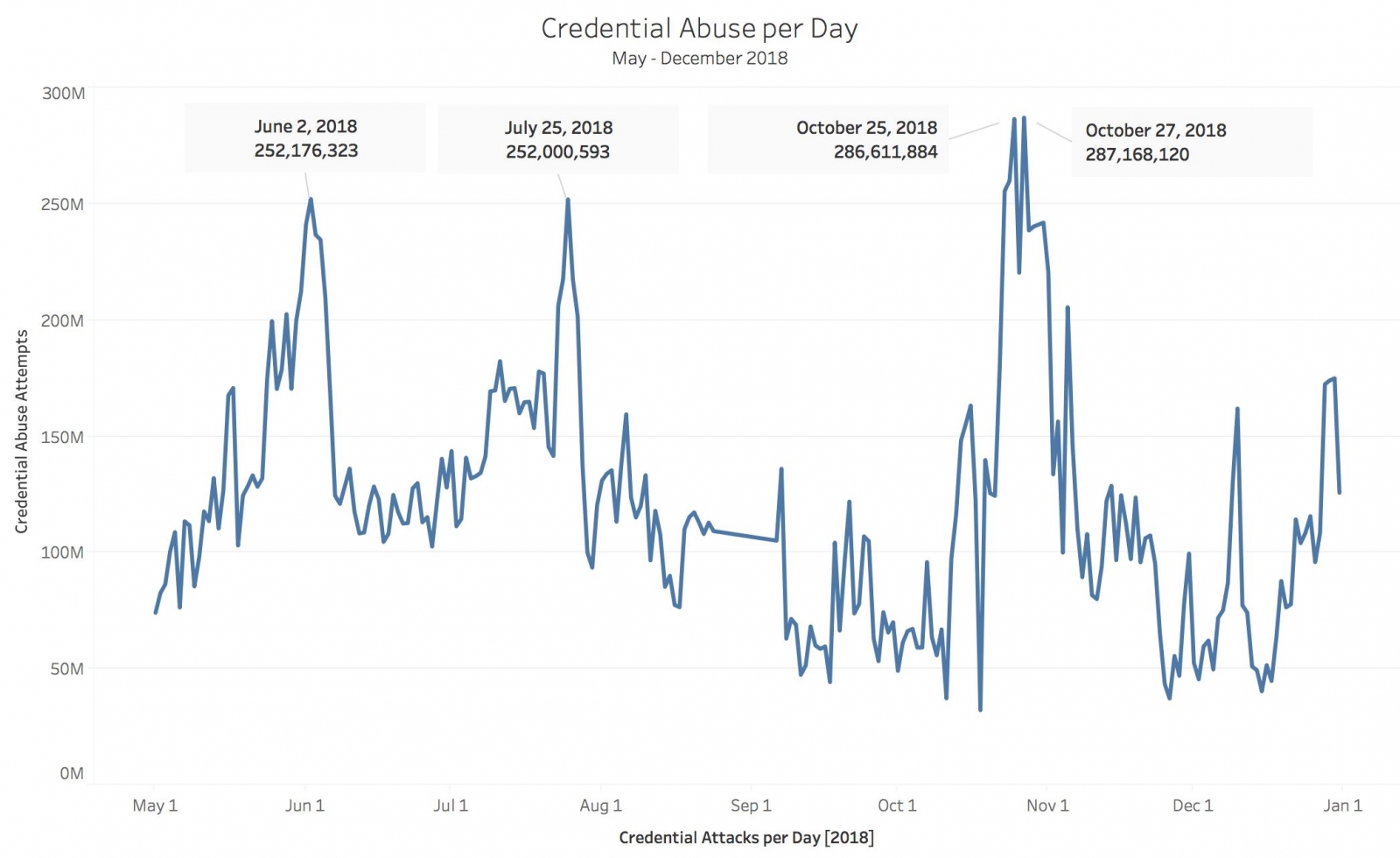
The Economy of Credential Stuffing Attacks
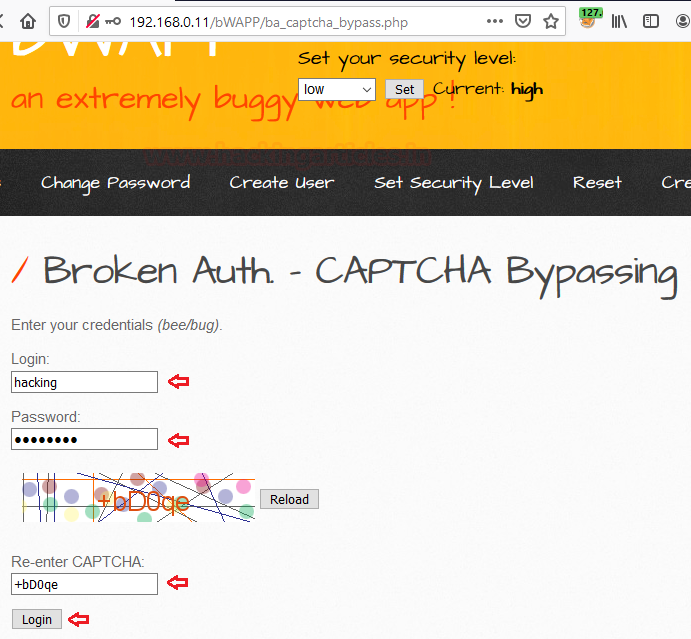
Comprehensive Guide on Broken Authentication & Session Management - Hacking Articles
Recomendado para você
-
 Best IP tracker to identify IP addresses easily06 março 2025
Best IP tracker to identify IP addresses easily06 março 2025 -
image-logger · GitHub Topics · GitHub06 março 2025
-
 Protect Yourself: Risks of Fake IPs, Free Proxies, and VPNs06 março 2025
Protect Yourself: Risks of Fake IPs, Free Proxies, and VPNs06 março 2025 -
 3 Ways to Get Someone's IP Address06 março 2025
3 Ways to Get Someone's IP Address06 março 2025 -
 IP Address Tracker - IP Tracker (Free Trial)06 março 2025
IP Address Tracker - IP Tracker (Free Trial)06 março 2025 -
Ps4 Ip Puller06 março 2025
-
IP Logger URL Shortener - Log and Track IP addresses06 março 2025
-
Free subdomain finder online 🛡️ find subdomains of domain06 março 2025
-
Someone sent me a link that had an IP grabber on it, I wanted to06 março 2025
-
![Xbox IP Finder How to Pull IPs on Xbox? [2023 Update] - MiniTool](https://www.partitionwizard.com/images/uploads/2022/08/xbox-ip-finder-thumbnail.jpg) Xbox IP Finder How to Pull IPs on Xbox? [2023 Update] - MiniTool06 março 2025
Xbox IP Finder How to Pull IPs on Xbox? [2023 Update] - MiniTool06 março 2025
você pode gostar
-
M.P.Street06 março 2025
-
 Roblox GIF - Roblox - Discover & Share GIFs06 março 2025
Roblox GIF - Roblox - Discover & Share GIFs06 março 2025 -
Mapas do CS 1.6 Relembre os Melhores Mapas do Jogo (PT)06 março 2025
-
 Newly discovered Resident Evil 4 Remake speedrun strats are also great for normal players06 março 2025
Newly discovered Resident Evil 4 Remake speedrun strats are also great for normal players06 março 2025 -
 Kit Jogos De Tabuleiro Xadrez/dama + Jogo De Cartas Uno06 março 2025
Kit Jogos De Tabuleiro Xadrez/dama + Jogo De Cartas Uno06 março 2025 -
 70+ Rin Nohara HD Wallpapers and Backgrounds06 março 2025
70+ Rin Nohara HD Wallpapers and Backgrounds06 março 2025 -
 Kohl's Stony Hill Tree Farm Susquehanna River Valley Visitors Bureau06 março 2025
Kohl's Stony Hill Tree Farm Susquehanna River Valley Visitors Bureau06 março 2025 -
 Deportivo Espanol Reserves vs Ferrocarril Midland Reserves» Predictions, Odds, Live Score & Streams06 março 2025
Deportivo Espanol Reserves vs Ferrocarril Midland Reserves» Predictions, Odds, Live Score & Streams06 março 2025 -
 New MAP - Proton Bus Simulator 2023 Gameplay06 março 2025
New MAP - Proton Bus Simulator 2023 Gameplay06 março 2025 -
 Senpai ga Uzai Kouhai no Hanashi - My Senpai is Annoying - 106 março 2025
Senpai ga Uzai Kouhai no Hanashi - My Senpai is Annoying - 106 março 2025


